EC-COUNCIL EC0-349 dumps - 100% Pass Guarantee!
Vendor: EC-COUNCIL
Certifications: EC-COUNCIL Certifications
Exam Name: Computer Hacking Forensic Investigator
Exam Code: EC0-349
Total Questions: 304 Q&As ( View Details)
Last Updated: Mar 19, 2025
Note: Product instant download. Please sign in and click My account to download your product.

- Q&As Identical to the VCE Product
- Windows, Mac, Linux, Mobile Phone
- Printable PDF without Watermark
- Instant Download Access
- Download Free PDF Demo
- Includes 365 Days of Free Updates
VCE
- Q&As Identical to the PDF Product
- Windows Only
- Simulates a Real Exam Environment
- Review Test History and Performance
- Instant Download Access
- Includes 365 Days of Free Updates
EC-COUNCIL EC0-349 Last Month Results
 95.6% Pass Rate
95.6% Pass Rate 365 Days Free Update
365 Days Free Update Verified By Professional IT Experts
Verified By Professional IT Experts 24/7 Live Support
24/7 Live Support Instant Download PDF&VCE
Instant Download PDF&VCE 3 Days Preparation Before Test
3 Days Preparation Before Test 18 Years Experience
18 Years Experience 6000+ IT Exam Dumps
6000+ IT Exam Dumps 100% Safe Shopping Experience
100% Safe Shopping Experience
EC0-349 Q&A's Detail
| Exam Code: | EC0-349 |
| Total Questions: | 304 |
| Single & Multiple Choice | 304 |
CertBus Has the Latest EC0-349 Exam Dumps in Both PDF and VCE Format
- EC-COUNCIL_certbus_EC0-349_by_Renuka_271.pdf
- 221.91 KB
- EC-COUNCIL_certbus_EC0-349_by_Azhar_from_Pakistan_274.pdf
- 222 KB
- EC-COUNCIL_certbus_EC0-349_by_Oladimeji_253.pdf
- 252.14 KB
- EC-COUNCIL_certbus_EC0-349_by_hayatou_258.pdf
- 221.52 KB
- EC-COUNCIL_certbus_EC0-349_by_Saied_247.pdf
- 231.41 KB
- EC-COUNCIL_certbus_EC0-349_by_Boone_268.pdf
- 221.39 KB
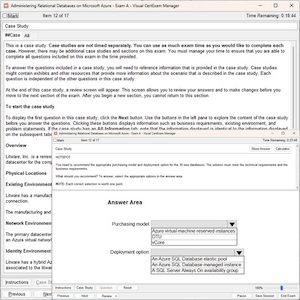
EC0-349 Online Practice Questions and Answers
What will the following command accomplish?
A. Test ability of a router to handle over-sized packets
B. Test the ability of a router to handle under-sized packets
C. Test the ability of a WLAN to handle fragmented packets
D. Test the ability of a router to handle fragmented packets
What type of flash memory card comes in either Type I or Type II and consumes only five percent of the power required by small hard drives?
A. SD memory
B. CF memory
C. MMC memory
D. SM memory
Sniffers that place NICs in promiscuous mode work at what layer of the OSI model?
A. Network
B. Transport
C. Physical
D. Data Link
Item 2If you come across a sheepdip machine at your client site, what would you infer?
A. A sheepdip coordinates several honeypots
B. A sheepdip computer is another name for a honeypot
C. A sheepdip computer is used only for virus-checking.
D. A sheepdip computer defers a denial of service attack
When monitoring for both intrusion and security events between multiple computers, it is essential that the computers' clocks are synchronized. Synchronized time allows an administrator to reconstruct what took place during an attack against multiple computers. Without synchronized time, it is very difficult to determine exactly when specific events took place, and how events interlace. What is the name of the service used to synchronize time among multiple computers?
A. Universal Time Set
B. Network Time Protocol
C. SyncTime Service
D. Time-Sync Protocol
Add Comments
Success Stories
- India
- LoL
- Mar 22, 2025
- Rating: 4.2 / 5.0
![]()
All this dumps are very good, i just did this one and took part in my exam. i really don't believe myself that i have got so high score. Thanks for their dumps.
- Spain
- Ned
- Mar 20, 2025
- Rating: 4.1 / 5.0
![]()
Passed full scored. I should let you know. The EC0-349 exam dump is very good, valid and accurate.
- Pakistan
- Aaron
- Mar 19, 2025
- Rating: 4.6 / 5.0
![]()
Now, I'm very happy that I have passed the EC0-349 exam in the morning. Thanks for my friend introducing the good dumps to me. I will also recommend the dumps to others.
- Morocco
- zouhair
- Mar 19, 2025
- Rating: 4.2 / 5.0
![]()
The content of this dumps is rich and complete, you can find that all the answers of questions from this dumps. Very useful.
- India
- Karl
- Mar 15, 2025
- Rating: 4.3 / 5.0
![]()
So happy. I passed the exam with the help of this material. Good luck to you.
- Singapore
- Zy
- Mar 15, 2025
- Rating: 4.7 / 5.0
![]()
At first, I don’t think I can pass the EC0-349 exam. But when I used this dumps, I felt more confident to pass the exam. It is not out of my expectation, i passed the exam with the full score because I met many same question that i have done in this dumps. Thanks these dumps, it is useful.
- United States
- Tom
- Mar 15, 2025
- Rating: 4.3 / 5.0
![]()
Recommend this EC0-349 exam dump to you strongly, really useful and convenient.
- United Arab Emirates
- BOBO
- Mar 14, 2025
- Rating: 5.0 / 5.0
![]()
I really felt surprised that i would pass the exam with so high score by using this dumps. I will share this good study material with my friends.
- United States
- Quentin
- Mar 14, 2025
- Rating: 4.4 / 5.0
![]()
Very good EC0-349 dumps, take full use of it, you will pass the exam just like me.
- New Zealand
- Quirita
- Mar 13, 2025
- Rating: 4.5 / 5.0
![]()
This dumps was introduced by my good friend several month ago. At first, I don't think it will help me a lot. But when I found many new questions that I never found from other study materials, i begun to pay more attention on this dumps. At last, I only used this dumps for preparing my exam. A moment ago, i have cleared that i passed the exam with almost full score. Thanks for this dumps, i will recommend to others just as my friend do.

 Printable PDF
Printable PDF