EC-COUNCIL 312-50V8 dumps - 100% Pass Guarantee!
Vendor: EC-COUNCIL
Certifications: EC-COUNCIL Certifications
Exam Name: Certified Ethical Hacker v8
Exam Code: 312-50V8
Total Questions: 1008 Q&As
Last Updated: Mar 15, 2025
Note: Product instant download. Please sign in and click My account to download your product.

- Q&As Identical to the VCE Product
- Windows, Mac, Linux, Mobile Phone
- Printable PDF without Watermark
- Instant Download Access
- Download Free PDF Demo
- Includes 365 Days of Free Updates
VCE
- Q&As Identical to the PDF Product
- Windows Only
- Simulates a Real Exam Environment
- Review Test History and Performance
- Instant Download Access
- Includes 365 Days of Free Updates
EC-COUNCIL 312-50V8 Last Month Results
 99.5% Pass Rate
99.5% Pass Rate 365 Days Free Update
365 Days Free Update Verified By Professional IT Experts
Verified By Professional IT Experts 24/7 Live Support
24/7 Live Support Instant Download PDF&VCE
Instant Download PDF&VCE 3 Days Preparation Before Test
3 Days Preparation Before Test 18 Years Experience
18 Years Experience 6000+ IT Exam Dumps
6000+ IT Exam Dumps 100% Safe Shopping Experience
100% Safe Shopping Experience
312-50V8 Q&A's Detail
| Exam Code: | 312-50V8 |
| Total Questions: | 1008 |
CertBus Has the Latest 312-50V8 Exam Dumps in Both PDF and VCE Format
- NetApp_certbus_312-50V8_by_White_Noise_871.pdf
- 234.34 KB
- NetApp_certbus_312-50V8_by_aftershow_972.pdf
- 221.53 KB
- NetApp_certbus_312-50V8_by_Night_857.pdf
- 231.25 KB
- NetApp_certbus_312-50V8_by_noname_884.pdf
- 255.16 KB
- NetApp_certbus_312-50V8_by_nowCCNP_953.pdf
- 224.76 KB
- NetApp_certbus_312-50V8_by_ccie_2_be_966.pdf
- 221.25 KB
312-50V8 Online Practice Questions and Answers
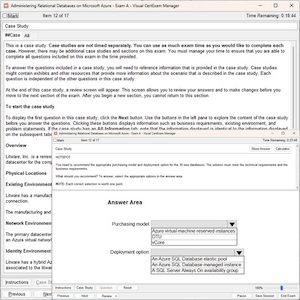
Which element of Public Key Infrastructure (PKI) verifies the applicant?
A. Certificate authority
B. Validation authority
C. Registration authority
D. Verification authority
When an alert rule is matched in a network-based IDS like snort, the IDS does which of the following?
A. Drops the packet and moves on to the next one
B. Continues to evaluate the packet until all rules are checked
C. Stops checking rules,sends an alert,and lets the packet continue
D. Blocks the connection with the source IP address in the packet
Which type of antenna is used in wireless communication?
A. Omnidirectional
B. Parabolic
C. Uni-directional
D. Bi-directional
Google uses a unique cookie for each browser used by an individual user on a computer.
This cookie contains information that allows Google to identify records about that user on its database.
This cookie is submitted every time a user launches a Google search, visits a site using AdSense etc. The
information stored in Google's database, identified by the cookie, includes.
How would you prevent Google from storing your search keywords?
A. Block Google Cookie by applying Privacy and Security settings in your web browser
B. Disable the Google cookie using Google Advanced Search settings on Google Search page
C. Do not use Google but use another search engine Bing which will not collect and store your search keywords
D. Use MAC OS X instead of Windows 7. Mac OS has higher level of privacy controls by default.
If you send a SYN to an open port, what is the correct response?(Choose all correct answers.)
A. SYN
B. ACK
C. FIN
D. PSH
Add Comments
Success Stories
- India
- Rudy
- Mar 16, 2025
- Rating: 4.5 / 5.0
![]()
Thanks for your help. I passed my exam yesterday with a high score. I think you have the great dumps. all my questions are from your materials. I'm very happy with that. Thanks.
- Pakistan
- August
- Mar 15, 2025
- Rating: 4.8 / 5.0
![]()
This dumps is valid, and this dumps is the only study material i used for this exam. Surprisingly i met the same question in the exam, so i passed the exam without doubt. Thanks for this dumps and i will recommend it to my friends.
- Greece
- Rhys
- Mar 15, 2025
- Rating: 5.0 / 5.0
![]()
update quickly and be rich in content, great dumps.
- United States
- Zouleha
- Mar 15, 2025
- Rating: 5.0 / 5.0
![]()
Update quickly and be rich in content,this dumps is really valid. Thanks.
- Saudi Arabia
- Alvin
- Mar 15, 2025
- Rating: 4.4 / 5.0
![]()
I'm so glad that I have chosen you as my assistant with my 312-50V8 exam. I passed my exam. Full scored. I will recommend to friends.
- South Africa
- Mickey
- Mar 14, 2025
- Rating: 4.3 / 5.0
![]()
A very good study material, i just used one month and i passed the exam yesterday. So you can trust on it.
- India
- Zumar
- Mar 14, 2025
- Rating: 4.6 / 5.0
![]()
I have passed the exam with their dumps. Thanks a million!
- Greece
- Ramon
- Mar 14, 2025
- Rating: 4.9 / 5.0
![]()
The answers are accurate. Well you should notice some of the questions are slightly changed. Be careful.
- Jordan
- zyd
- Mar 13, 2025
- Rating: 4.9 / 5.0
![]()
There are so many new questions in the latest update. You can trust on this. Good luck to you all, guys.
- United States
- zzz
- Mar 13, 2025
- Rating: 4.5 / 5.0
![]()
i must recommend this dumps to you for i achieved full score with the help of it. i believe that you can do it like me by using this dumps.

 Printable PDF
Printable PDF