SC-900 Online Practice Questions and Answers
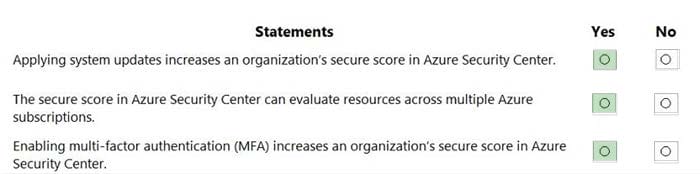
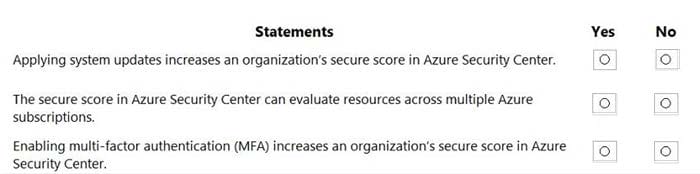
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area:
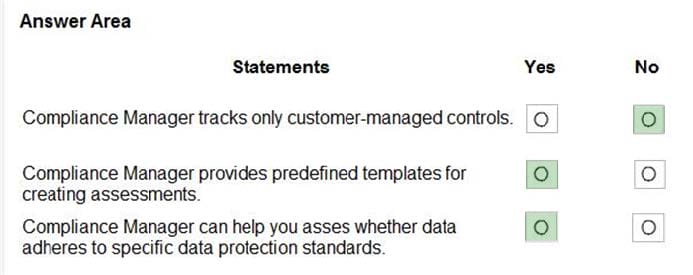
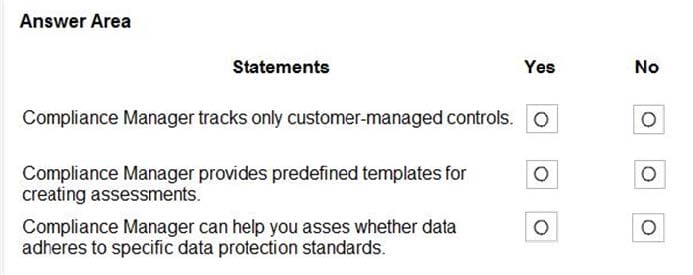
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area:
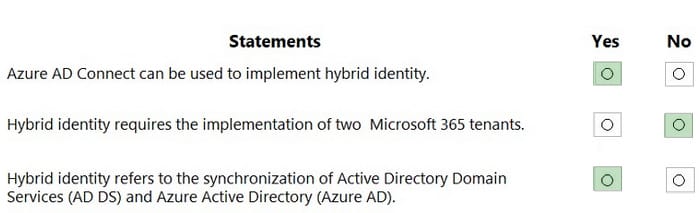
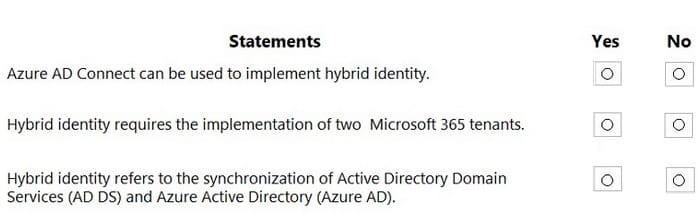
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area:
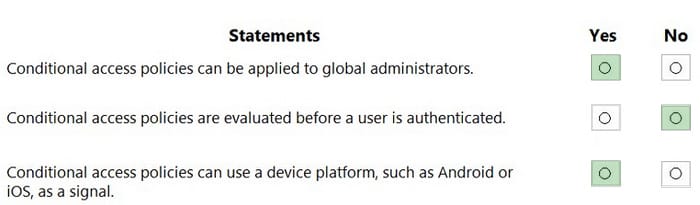
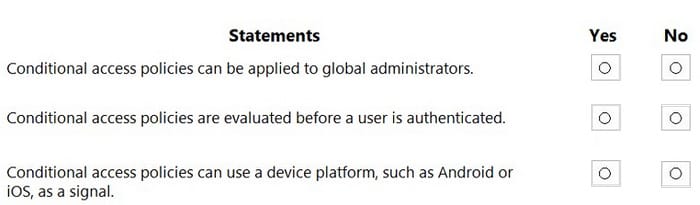
HOTSPOT
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area:
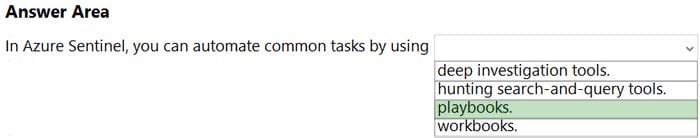
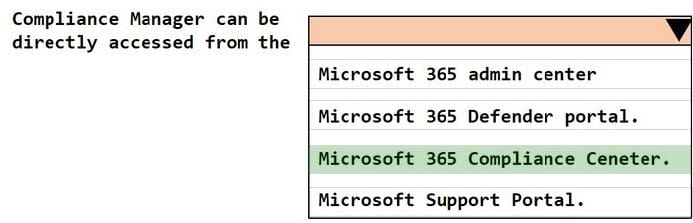
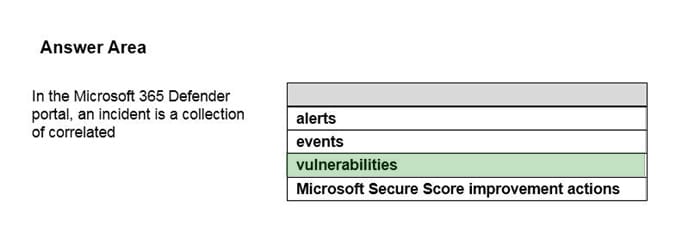
HOTSPOT
Select the answer that correctly completes the sentence.
Hot Area:
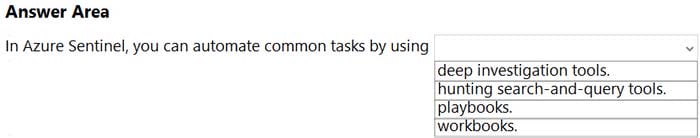
HOTSPOT
Select the answer that correctly completes the sentence.
Hot Area:

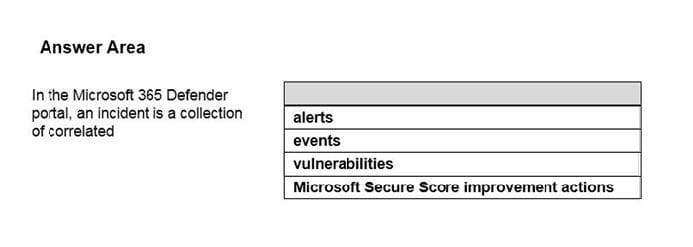
HOTSPOT
Select the answer that correctly completes the sentence.
Hot Area:
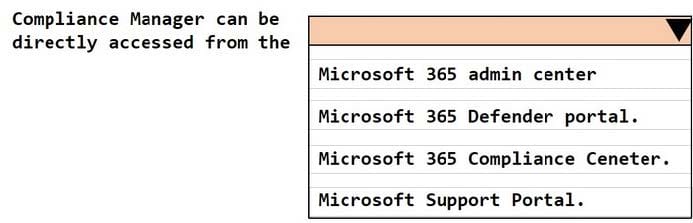
HOTSPOT
Select the answer that correctly completes the sentence.
Hot Area:
Which Azure Active Directory (Azure AD) feature can you use to evaluate group membership and automatically remove users that no longer require membership in a group?
A. access reviews
B. managed identities
C. conditional access policies
D. Azure AD Identity Protection
What can you use to provision Azure resources across multiple subscriptions in a consistent manner?
A. Azure Defender
B. Azure Blueprints
C. Azure Sentinel
D. Azure Policy
Which compliance feature should you use to identify documents that are employee resumes?
A. pre-trained classifiers
B. Content explorer
C. Activity explorer
D. eDiscovery
What are customers responsible for when evaluating security in a software as a service (SaaS) cloud services model?
A. applications
B. network controls
C. operating systems
D. accounts and identities
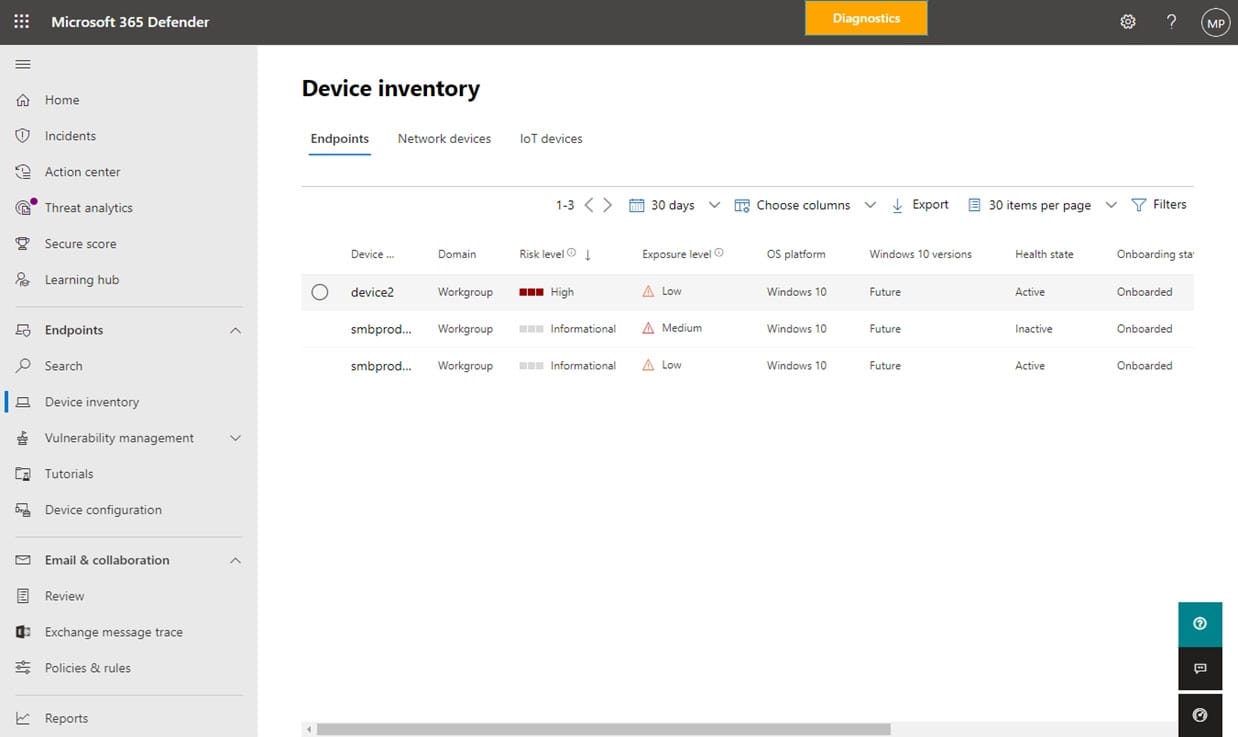
Which two cards are available in the Microsoft 365 Defender portal? Each correct answer presents a complete solution. NOTE: Each correct selection is worth one point.
A. Devices at risk
B. Compliance Score
C. Service Health
D. User Management
E. Users at risk
What can you use to deploy Azure resources across multiple subscriptions in a consistent manner?
A. Microsoft Sentinel
B. Microsoft Defender for Cloud
C. Azure Policy
D. Azure Blueprints
What should you use to associate the same identity to more than one Azure virtual machine?
A. an Azure AD user account
B. a user-assigned managed identity
C. a system-assigned managed identity
D. an Azure AD security group