NSE6_FNC-8.5 Online Practice Questions and Answers
Which two of the following are required for endpoint compliance monitors? (Choose two.)
A. Logged on user
B. Security rule
C. Persistent agent
D. Custom scan
By default, if more than 20 hosts are seen connected on a single port simultaneously, what will happen to the port?
A. The port is added to the Forced Registration group.
B. The port is disabled.
C. The port is switched into the Dead-End VLAN.
D. The port becomes a threshold uplink.
In which view would you find who made modifications to a Group?
A. The Admin Auditing view
B. The Alarms view
C. The Event Management view
D. The Security Events view
What causes a host's state to change to "at risk"?
A. The host has been administratively disabled.
B. The logged on user is not found in the Active Directory.
C. The host has failed an endpoint compliance policy or admin scan.
D. The host is not in the Registered Hosts group.
What capability do logical networks provide?
A. VLAN-based inventory reporting
B. Interactive topology view diagrams
C. Application of different access values from a single access policy
D. Autopopulation of device groups based on point of connection
Refer to the exhibit.
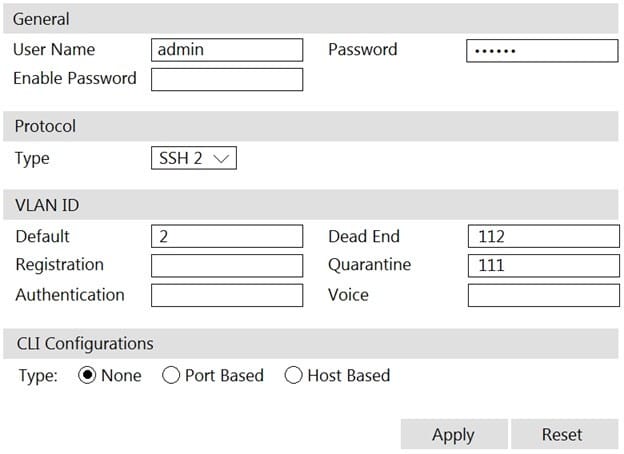
If you are forcing the registration of unknown (rogue) hosts, and an unknown (rogue) host connects to a port on the switch, what will occur?
A. No VLAN change is performed.
B. The host is disabled.
C. The host is moved to VLAN 111.
D. The host is moved to a default isolation VLAN.
How are logical networks assigned to endpoints?
A. Through Layer 3 polling configurations
B. Through network access policies
C. Through FortiGate IPv4 policies
D. Through device profiling rules
What would occur if both an unknown (rogue) device and a known (trusted) device simultaneously appeared on a port that is a member of the Forced Registration port group?
A. The port would be provisioned to the registration network, and both hosts would be isolated.
B. The port would not be managed, and an event would be generated.
C. The port would be provisioned for the normal state host, and both hosts would have access to that VLAN.
D. The port would be administratively shut down.
