JN0-1361 Online Practice Questions and Answers
Exhibit:
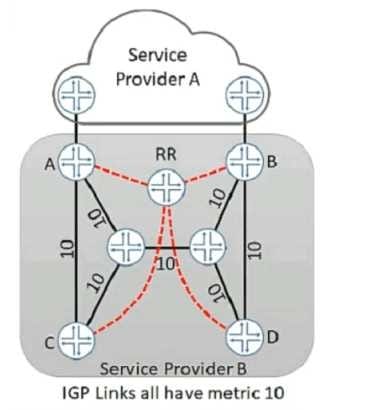
You work for service provider B that wants to implement a hot potato routing policy on the network so that router C uses link C-A to reach service provider A's advertised routes and router D uses link D- B to reach Service Provider A's advertised routes Currently traffic from router C is traversing the core to exit the network on router B . Referring to the exhibit, what are two design actions that would satisfy the requirements? (Choose two.)
A. Implement BGP-ORR
B. Configure new IBGP neighbors between routers C and A and routers D and B
C. Implement BGP-LS
D. Configure the route reflector to send multiple copies of a route learned from different IBGP peers to its clients.
Your customer is paying for traffic prioritization and you must ensure that all traffic from their 172.27.
10.0/24 network receives top priority through your network.
Which action will satisfy this requirement?
A. Apply a behavior aggregate classifier to the egress interface.
B. Apply a custom rewrite rule to the ingress interface.
C. Apply a multifield classifier to the ingress interfaces.
D. Apply a custom scheduler map to the ingress interface.
Your company is designing a new data center in a remote location that must be connected to your local data center. You have a service provider connection between the CE devices at each site. You want to implement EVPN with VXLAN services between sites, but the service provider does not offer EVPN services. Which two statements are true in this scenario? (Choose two )
A. The provider's edge devices must map your VXLAN VNIs to MPLS LSPs within the provider network at each site
B. The customer's edge devices within your data center can act as VXLAN Layer 2 gateways
C. You can still implement EVPN service across the service provider as long as there is IP reachability between the sites.
D. The service provider must provide an MPLS-based VPN connection between sites
Your applications are migrating from a legacy data center to an EVPN over a VXLAN-based VM environment. A few critical legacy applications not support this environment and must remain on bare metal servers and the applications must be able to access the Internet. What must be included in the VXLAN design to satisfy these requirements?
A. VTEP tunneling
B. VXLAN gateway
C. SR-IOV
D. nested VM capability
Exhibit: You are asked to ensure that most traffic that traverses your network is load balanced over all of the equal cost links between the routers in your network. However, you must also ensure that traffic from ISP A that is destined for ISP D must traverse the R1-R2-R3-R4-R5 path. Referring to the exhibit how would you accomplish this task?
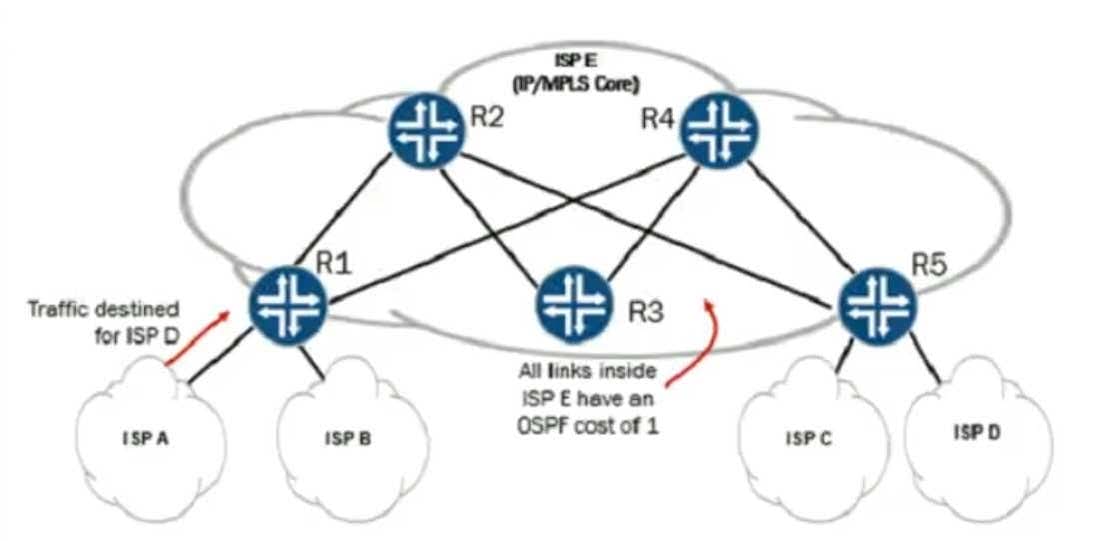
A. Force the ISP A to ISP D traffic over RSVP-signaled LSPs.
B. Adjust the BGFs LOCAL PREF attribute to ensure that the raw IP packets follow the required path.
C. Adjust the OSPF metrics of each link so that the raw IP packets follow the required path.
D. Force the ISP A to ISP D traffic over LDP-signaled LSPs.
Which two statements about BFD are correct? (Choose two)
A. BFD provides link failure detection for static routes.
B. BFD modifies each protocol timer to improve link failure detection.
C. NSR maintains BFD sessions during Routing Engine switchover.
D. GRES is required for BFD sessions to be established.
Your customer's enterprise is adding geographically-dispersed branch offices and requires new WAN
connections. The primary design consideration for this expansion is low cost but the branches must remain
secure with low latency.
Which type of Internet access model satisfies the customer's requirement in this scenario?
A. distributed model with security at the hub
B. centralized model with security at the hub
C. centralized model with security at each branch
D. distributed model with security at each branch
Your customer wants to use NorthStar to communicate with network devices and acquire the MPLS topology. Which protocol is recommended for this purpose?
A. PIM-SSM
B. OSPF
C. BGP-LS
D. ISIS
You are asked to improve the convergence time in your large enterprise WAN Each branch office network
is multihomed to two central aggregation points using BGP.
Which action would satisfy the requirement?
A. Provision more WAN bandwidth.
B. Increase interface hold timers.
C. Decrease interface hold timers.
D. Use Bidirectional Forwarding Detection.
Click the Exhibit button Referring to the network design shown in the exhibit, you must ensure that VPN data between Site1 and Site2 will be earned over a single end-to-end LSP. How would you advertise PE1's loopback address to accomplish this task?
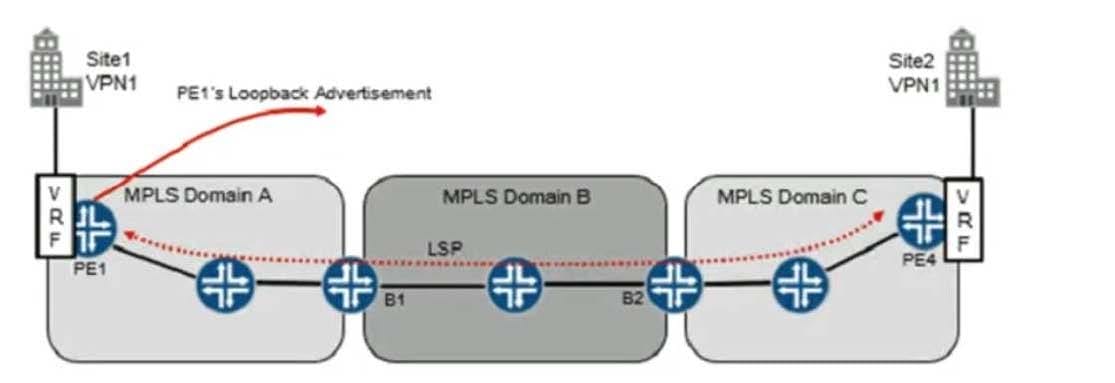
A. over a single MP-IBGP session (L3VPN NLRI) between PE1/PE4
B. over BGP-LU sessions between the PE1/B1. B1/B2 and B2/PE4
C. over a single IBGP session (IPv4 unicast NLRI) between PE VPE4
D. over a single EBGP session (IPv4 unicast NLRI) between PE1/PE4
Which management platform automates and simplifies the management of Juniper Networks switching, routing, and security products?
A. Junos Space
B. Juniper Secure Analytics
C. Junosphere
D. Junoscope
Your customer requires virtual machine mobility between two data centers, and they are pursuing a managed service. Which solution would satisfy the customer's requirement?
A. an EVPN service provided over IP
B. an L3VPN service
C. a routed service
D. an IPsec VPN service between CE routers
Your client asked you to design a solution with the requirements shown below.
Have better traffic engineering for applications across an existing MPLS core.
Support both IPv4 and IPv6 traffic
Work with an MX Series core.
Work with a North Star Controller
Work with existing IGP (ISIS)
Which feature would you recommend be implemented in this solution?
A. zero touch provisioning
B. segment routing
C. CoS-based forwarding
D. opaque area LSAs
You work for a service provider that offers L3VPN services to its customers. While designing L3VPN
solutions for customers, you sometimes need to share routes between routing instances as part of the
design.
What are two reasons for sharing routes between routing-instances? (Choose two)
A. so customers can reach the Internet
B. to allow the service provider's OoB network to be reachable by customers
C. so customers can reach the service provider's public cloud infrastructure
D. to support network address translation
Your customer requires redundant routers and wants to use VRRP for the default gateway at their Internet edge. Which two statements are correct in this scenario? (Choose two )
A. VRRP will only support two routers
B. The VRRP master and backup send advertisements to each other at regular intervals.
C. VRRP dynamically elects master and backup routers
D. VRRP for IPv6 provides a much faster switchover to an alternate default router than IPv6 neighbor discovery procedures
