FORTISANDBOX Online Practice Questions and Answers
Which is true regarding Microsoft Office on FortiSandbox?
A. Microsoft Word documents (.docx) are not inspected.
B. Office 365 files are not supported.
C. Microsoft Office is not included. You must purchase it separately, then manually install it in the applicable VMs on FortiSandbox.
D. Office 2013 is installed in one of the VMs.
Which devices can be configured to send files to FortiSandbox 2.0.3? (Choose two.)
A. FortiGate
B. FortiMail
C. FortiSwitch
D. FortiAP
Which methods can be used to submit files to FortiSandbox for inspection? (Choose two.)
A. File shares
B. FTP upload
C. SFTP upload
D. JSON API
Which protocols can a FortiSandbox inspect when is deployed in sniffer mode? (Choose two.)
A. MAPI
B. FTPS
C. HTTP
D. POP3
Which protocols can FortiSandbox use to connect to a network file share? (Choose two.)
A. FTP
B. HTTP
C. NFSv2
D. CIFS
When does a FortiSandbox categorize a file as suspicious?
A. When the file is detected as known greyware
B. When the file matches an antivirus signature that might detect false positives
C. When the file matches a signature in the extended antivirus database
D. When the file is not detected as a known malware, but it has some of the same behaviors as malware
Which browser is installed in the Windows 7 x86 VM image?
A. Internet Explorer 9
B. Firefox
C. Google Chrome
D. Internet Explorer 10
What is the minimum FortiAnalyzer firmware version that supports FortiSandbox device registration?
A. 5.0.6
B. 5.0.11
C. 5.0.8
D. 5.2.1
FortiGate is configured to send suspicious files to a FortiSandbox for in-line inspection. The administrator
creates a new VDOM, and then generates some traffic so what the new VDOM sends a file to the
FortiSandbox for the first time.
Which is true regarding this scenario?
A. FortiSandbox will store the file, but not inspect it until the administrator manually authorizes the new VDOM.
B. Before generating traffic, the administrator can push the VDOM configuration from the FortiGate to the FortiSandbox. Then when FortiSandbox receives the file, FortiSandbox will inspect the file.
C. FortiSandbox can be pre-configured to automatically authorize the new VDOM and inspect the file.
D. FortiSandbox will store the file, but not inspect it until the administrator manually adds the new VDOM to the FortiSandbox configuration.
You can configure FortiGate and FortiMail to send potentially malicious files to FortiSandbox. Which file types are considered to be potentially malicious? (Choose three.)
A. JPEG images
B. Rich text format (RTF)
C. Adobe PDF
D. Adobe Flash
E. Microsoft PowerPoint
Which FortiGate process sends files to FortiSandbox for inspection?
A. scanunit
B. fortisandboxd
C. miglogd
D. quarantine
What mechanism does FortiGate use to avoid sending a file that has been already inspected to FortiSandbox?
A. FortiGate sends the file name to FortiGuard. FortiGuard checks if a file with that name has been already inspected.
B. FortiGate sends the file name to FortiSandbox. FortiSandbox checks if it has already inspected a file with that name.
C. FortiGate sends a hash of the file to FortiSandbox. FortiSandbox checks if it has already inspected a file with that hash.
D. FortiGate searches its cache of a list of file names that it has already inspected.
Which are true about activating the Microsoft Office license in a FortiSandbox? (Choose two.)
A. Happens simultaneously with the activation of the Windows licenses
B. Does not require Internet access
C. Requires that you download a license file from the Fortinet support website
D. Requires you to enter the key in the FortiSandbox GUI
Which protocols are supported for archiving scan job reports? (Choose two.)
A. CIFS
B. NFSv2
C. SMB
D. FTP
Based on the exhibit, which files will be sent to FortiSandbox? (Choose three.)
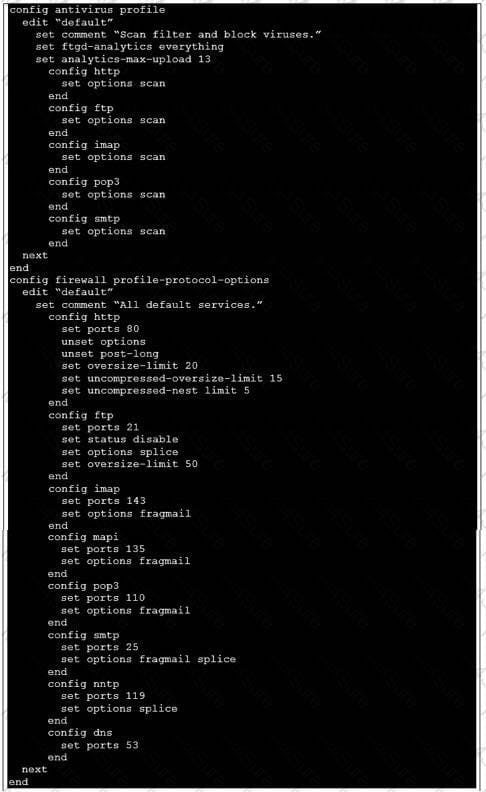
A. A 7 MB PDF attachment to an email, sent over SMTP.
B. A 3 MB archive that decompresses to 16 MB, sent over HTTP.
C. A 3 MB Flash video, sent over HTTP.
D. An 11 MB EXE file, sent of HTTP, detected as suspicious.
E. A 5 MB EXE file attached to an email, sent over POP3, detected as known malware.
