DCA Online Practice Questions and Answers
Which command interactively monitors all container activity in the Docker engine?
A. docker system logs
B. docker system events
C. docker container events
D. docker container logs
The following Docker Compose file is deployed as a stack:
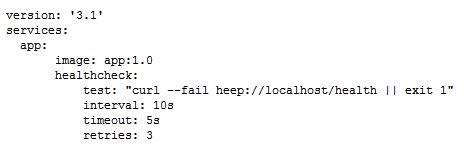
Is this statement correct about this health check definition?
Solution: Health checks test for app health ten seconds apart. Three failed health checks transition the container into "unhealthy" status.
A. Yes
B. No
Is this a Linux kernel namespace that is disabled by default and must be enabled at Docker engine runtime to be used? Solution: user
A. Yes
B. No
You configure a local Docker engine to enforce content trust by setting the environment variable
DOCKER_CONTENT_TRUST=1.
If myorg/myimage: 1.0 is unsigned, does Docker block this command?
Solution: docker service create myorg/myimage:1.0
A. Yes
B. No
You are troubleshooting a Kubernetes deployment called api, and want to see the events table for this object.
Does this command display it?
Solution: kubectl describe deployment api
A. Yes
B. No
Which statement is correct about cluster management in Docker Enterprise Edition 3.x?
A. Clusters can contain Windows 10 and Windows Server 2016 only.
B. Clusters can contain Linux, Windows Server 2016 and 2019, and Linux on IBM z Systems.
C. Clusters can contain Linux only.
D. Clusters can contain Linux and Windows Server 2008 R2 only.
When seven managers are in a swarm cluster how would they be distributed across three datacenters or availability zones?
A. 5-1-1
B. 3-2-2
C. 3-3-1
D. 4-2-1
Is this a type of Linux kernel namespace that provides container isolation? Solution: Storage
A. Yes
B. No
Are these conditions sufficient for Kubernetes to dynamically provision a persistentVolume, assuming there are no limitations on the amount and type of available external storage? Solution: A default provisioner is specified, and subsequently a persistentVolumeClaim is created.
A. Yes
B. No
In the context of a swarm mode cluster, does this describe a node? Solution: a physical machine participating in the swarm
A. Yes
B. No
A server is running low on disk space. What command can be used to check the disk usage of images, containers, and volumes for Docker engine?
A. 'docker system df'
B. 'docker system prune'
C. 'docker system free'
D. 'docker system ps'
The Kubernetes yaml shown below describes a networkPolicy.
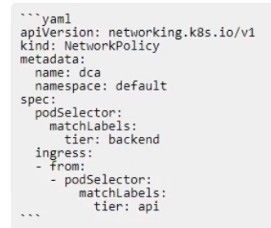
Will the networkPolicy BLOCK this traffic?
Solution: a request issued from a pod bearing the tier: backend label, to a pod bearing the tier: frontend label
A. Yes
B. No
Is this a supported user authentication method for Universal Control Plane? Solution: PAM
A. Yes
B. No
Two development teams in your organization use Kubernetes and want to deploy their applications while ensuring that Kubernetes-specific resources, such as secrets, are grouped together for each application.
Is this a way to accomplish this?
Solution: Create one pod and add all the resources needed for each application
A. Yes
B. No
Can this set of commands identify the published port(s) for a container? Solution: `docker container inspect", docker port'
A. Yes
B. No
