CIS-SIR Online Practice Questions and Answers
Using the KB articles for Playbooks tasks also gives you which of these advantages?
A. Automated activities to run scans and enrich Security Incidents with real time data
B. Automated activities to resolve security Incidents through patching
C. Improved visibility to threats and vulnerabilities
D. Enhanced ability to create and present concise, descriptive tasks
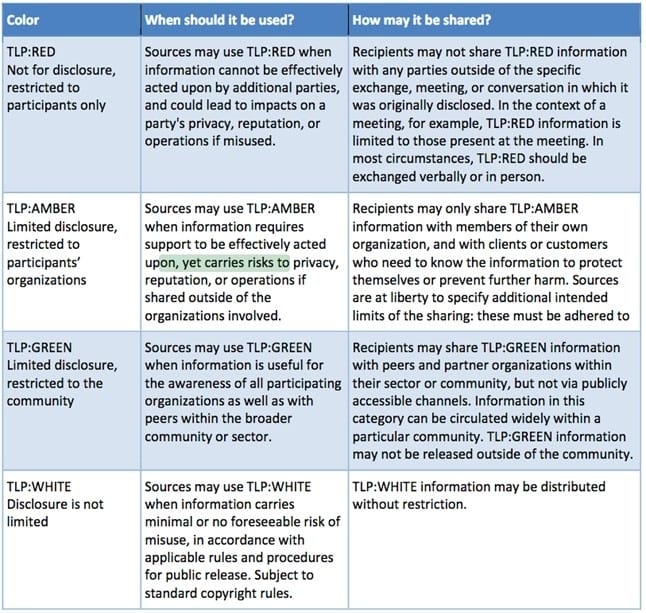
Security tag used when a piece of information requires support to be effectively acted upon, yet carries risks to privacy, reputation, or operations if shared outside of the organizations involved.
A. TLP:GREEN
B. TLP:AMBER
C. TLP:RED
D. TLP:WHITE
What is the purpose of Calculator Groups as opposed to Calculators?
A. To provide metadata about the calculators
B. To allow the agent to select which calculator they want to execute
C. To set the condition for all calculators to run
D. To ensure one at maximum will run per group
Select the one capability that retrieves a list of running processes on a CI from a host or endpoint.
A. Get Network Statistics
B. Isolate Host
C. Get Running Processes
D. Publish Watchlist
E. Block Action
F. Sightings Search
What is calculated as an arithmetic mean taking into consideration different values in the CI, Security Incident, and User records?
A. Priority
B. Business Impact
C. Severity
D. Risk Score
What three steps enable you to include a new playbook in the Selected Playbook choice list? (Choose three.)
A. Add the TLP: GREEN tag to the playbooks that you want to include in the Selected Playbook choice list
B. Navigate to the sys_hub_flow.list table
C. Search for the new playbook you have created using Flow Designer
D. Add the sir_playbook tag to the playbooks that you want to include in the Selected Playbook choice list
E. Navigate to the sys_playbook_flow.list table
Joe is on the SIR Team and needs to be able to configure Territories and Skills. What role does he need?
A. Security Basic
B. Manager
C. Security Analyst
D. Security Admin
The following term is used to describe any observable occurrence:.
A. Incident
B. Log
C. Ticket
D. Alert
E. Event