CBSP Online Practice Questions and Answers
Which blockchain security control either risks centralization or permanently divergent chains?
A. Random Neighbor Selection
B. Permissioned Blockchains
C. Checkpoints
D. Private Blockchains
Which smart contract vulnerability allows an attacker to make a profit off a smart contract cryptocurrency exchange like Bancor?
A. Arithmetic
B. Access Control
C. Race Conditions
D. Reentrancy
Which of the following are common inputs to the algorithm to select the next block creator in Proof of Stake? Select all that apply
A. Age of User Account
B. Time Since Last Chosen to Create a Block
C. Stake Size
D. User Activity on the Blockchain
Which algorithm was adopted by Bitcoin's creator for use as a consensus mechanism?
A. Proof of Stake
B. Proof of Space
C. Proof of Work
D. Proof of Activity
For which of the following regulatory requirements is blockchain technology best suited?
A. Data Control
B. Data Retention
C. Transparency
D. Data Deletion
Both sidechains and slate channels rely on the original blockchain for security and as a fallback if issues occur.
A. True
B. False
Which of the following attacks is designed to bypass the protections provided by digital signatures?
A. Routing
B. Replay
C. Sybil
D. Eclipse
Proof of Work never guarantees that the blockchain network has reached consensus.
A. True
B. False
Which of the following blockchain consensus algorithms is the most sustainable long-term?
A. Proof of Stake
B. Proof of Work
C. Proof of Burn
D. Proof of Space
A major advantage of a stale channel is that it provides a permanent means of transferring value between two parties.
A. True
B. False
This sample code is vulnerable to which of the following attacks? Select all that apply A. Arithmetic
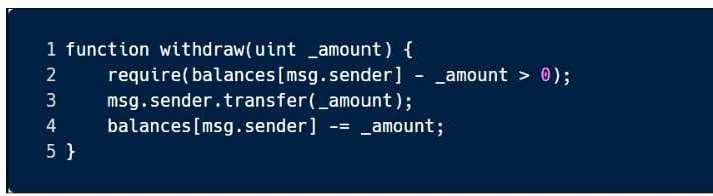
B. Race Conditions
C. Unchecked Return Values
D. Short Addresses
Spinning up a large number of temporary mining servers is likely part of what type of attack?
A. Routing
B. Denial of Service
C. Sybil
D. Eclipse
Sidechains can benefit the mainchain in what ways? Select all that apply
A. Speed
B. Functionality
C. Scalability
D. Security
Using a distributed ledger decreases risk of data loss since all data is not stored in the same place.
A. True
B. False
Transaction validation on DAG-based DLTs is designed in a way that allows legitimate transactions to be considered untrusted due to random chance.
A. True
B. False
