ACMP_6.4 Online Practice Questions and Answers
Which of the following firewall rules allows a user to initiate an ICMP session to other devices?(Choose two)
A. localip any svc-icmp permit
B. user any svc-icmp permit
C. user user svc-icmp permit
D. any any svc-icmp permit
E. mswitch any svc-icmp permit
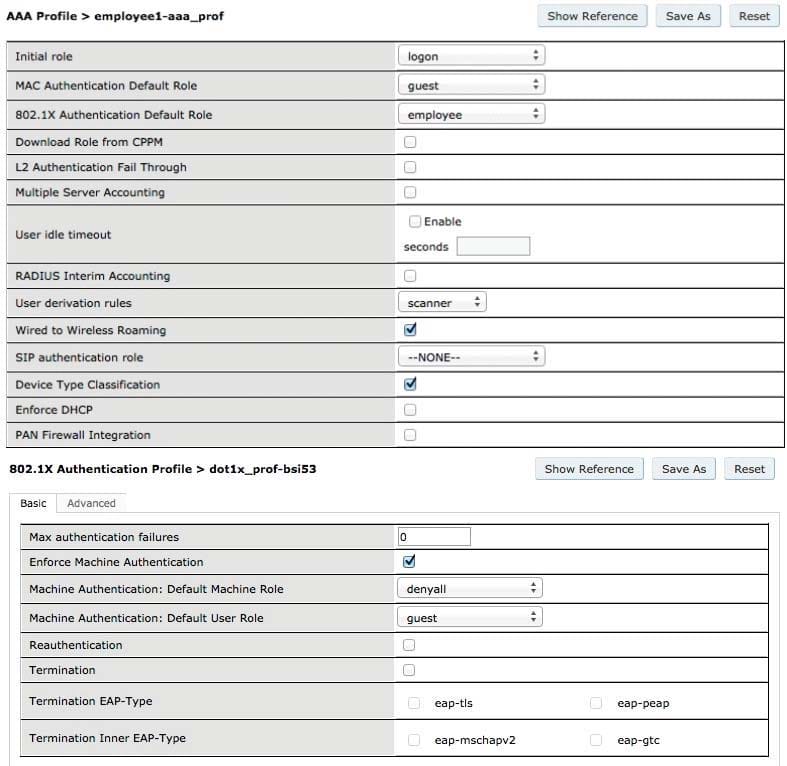
The screen captures above show the 802.1X authentication profile and AAA profile settings for a VAP. Ifmachineauthenticationfailsanduserauthenticationpasses, whichrolewillbeassigned?
A. employee
B. guest
C. denyall
D. logon
E. no role is assigned
As an admin/root user, what other type of role-based management users can be created on Aruba controllers?
A. Auditing-compliance user
B. AirWave management user
C. Reporting Generationuser
D. Guest provisioning user
E. Maintenance user
By default, how long will an AP scan a single channel when ARM is enabled?
A. 80 milliseconds
B. 90 milliseconds
C. 100 milliseconds
D. 110 milliseconds
E. 200 milliseconds
What is the function of Band Steering?
A. Balancing clients across APs on different channels within the same band
B. Encouragesclients, 5GHz capable, to connecton the 5GHzspectrum
C. Coordinate access to the same channel across multiple APs
D. Enables selection of 20 vs. 40 MHz mode of operation per band
E. Enables acceptable coverage index on both the "bjg" and "a" spectrums
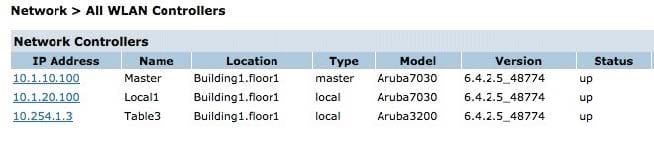
Referring to the above screen capture, on which Controller can you create a VLAN?
A. Controller 10.1.10.100 only
B. Controller 10.1.20.100 and 10.254.1.3 only
C. All three Controllers D. None of the Controllers
E. Controller 10.254.1.101 only
Screenshots of the Captive Portal authentication profile and server group of a guest network are displayed
above.
How was the user authenticated?
A. with a radius server called Radius01
B. with the Internal database
C. with a radius server called Internal
D. with another form of authentication
E. user wasn't authenticated against any server
How many Aruba controllers can be added to a single mobility domain?
A. 64 controllers of any type
B. 128 controllers supporting 2000 users
C. 256 controllers with no more than 1024 subnets
D. Controllers supporting up to 6000 AP's
E. There is no controller limit
A university, has 2 departments. Department 1 has its own mobility domain with one controller. Department
2 has multiple controllers configured in a second domain. The university is planning on offering a new
application and needs users to be able to roam between both mobility domains.
What is the best way to accomplish this?
A. The 2 existing domains should be left as they are. A 3rd mobility domain should then be created and all 3 controllers need to be added to it
B. Merge the controllers into the same mobility domain
C. The IP subnets of all controllers need to be configured to match
D. This cannot be accomplished
E. Create a new domain between a department 1 controller and one of the department 2 controllers
An AP is not communicating with the controller. Upon investigation you find that the AP is not discovering its controller through DNS. Instead, it received a DHCP reply with option 43 specifying the SIP server's IP address. How do you resolve this problem?
A. Statically configure the AP to ignore Option 43
B. On the DHCP server implement Option 60 C. Statically configure the AP to only use DNS resolution and no other dynamic discovery methods
D. After failing option 43 the AP should have proceeded with ADP, therefore the AP is faulty and needs to be replaced
E. The AP should be purged
(group8) #show ap arm history ap-name AP1 Interface :wifi0 ARM History
Time of Change Old Channel New Channel Old Power New Power Reason -------------- ----------- ------------------- --------- ------ 2015-1-28 07:58:53 157+ 149+ 21 21 I 2015-1-28 07:52:06 149+ 157+ 21 21 M 2015-1-28 07:16:59 157+ 149+ 21 21 I
Interface :wifi1 ARM History
Time of Change Old Channel New Channel Old Power New Power Reason -------------- ----------- ------------------- --------- ------ 2015-1- 28 08:52:53 6 1 21 21 I Referring to the output above. What can you conclude about AP1?
A. This device is scanning channels.
B. This device is unstable because the channel assignment changed.
C. The device changed channels recently.
D. The device changed channels and power levels recently.
E. The device is transmitting at maximum power levels.
Which of the following parameters can be specified in a rule for AP classification? (Choose three) A. SSID of an AP
B. Number of clients connected to an AP.
C. SNR of an AP.
D. Operating mode of an AP
E. Discovering APs
Which of the following functions can be configured in the Controller WIP wizard? (Choose three.)
A. Configure APs as Air Monitors
B. Configure rules for AP classification.
C. Configure preset levels for intrusion detection
D. Blacklisting Rules for clients
E. Identify encryption method used in your network.
Which of the following describes a Remote AP provisioned in "Split-Tunnel" Forwarding mode?.
A. Local user traffic first goes to the controller and is then spilt back to the local network.
B. All data and control traffic goes to the controller unsecured.
C. The user role must have a "Permit" statement in order to locally bridge the traffic.
D. The user role must have a "route src-nat" statement to locally bridge the traffic.
E. The RAP uses PAPI to send data traffic to the controller.
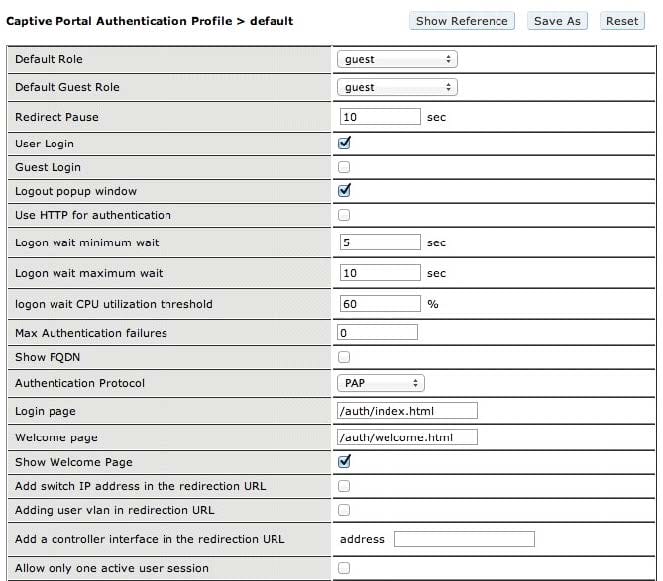
A user logged in with the Captive Portal settings shown in the above screen capture. What does the user need to do to logout?
A. wait 30 minutes then logout
B. wait 60 minutes then logout
C. click Logout on the browser screen
D. he cannot logout
E. wait 10 seconds for redirect
