500-220 Online Practice Questions and Answers
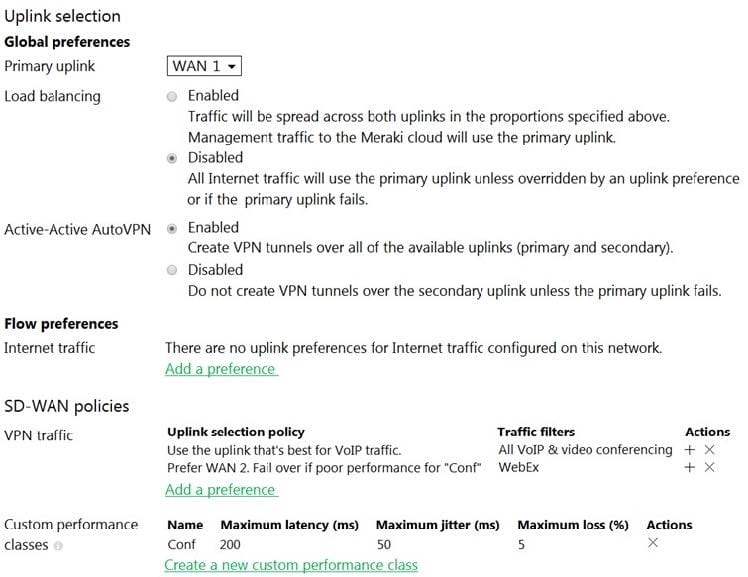
Refer to the exhibit. Assuming this MX has established a full tunnel with its VPN peer, how will the MX route the WebEx traffic?
A. WebEx traffic will prefer WAN 2 as long as it meets the thresholds in the "Conf" performance class.
B. WebEx traffic will prefer WAN 1 as it is the primary uplink.
C. WebEx traffic will prefer WAN 2 as long as it is up.
D. WebEx traffic will be load-balanced between both active WAN links.
Company iPads are enrolled in Systems Manager without supervision, and profiles are pushed through Systems Manager.
Which outcome occurs when a user attempts to remove the "Meraki Management" profile on an iPad?
A. The "Meraki Management" profile cannot be removed.
B. The "Meraki Management" profile is removed and then pushed automatically by Systems Manager.
C. The "Meraki Management" profile is removed. All the profiles that Systems Manager pushed are also removed.
D. The "Meraki Management" profile is removed. All the profiles Systems Manager pushed remain.
What occurs when a configuration change is made to an MX network that is bound to a configuration template?
A. The configuration change in the bound network is combined with the template configuration inside the template.
B. The more restrictive configuration is preferred.
C. The configuration change in the bound network overrides the template configuration.
D. The template configuration overrides the configuration change in the bound network.
One thousand concurrent users stream video to their laptops. A 30/70 split between 2.4 GHz and 5 GHz is used. Based on client count, how many APs (rounded to the nearest whole number) are needed?
A. 26
B. 28
C. 30
D. 32

Refer to the exhibit. This Dashboard organization uses Co-Termination licensing model.
What happens when an additional seven APs are claimed on this network without adding licenses?
A. All APs immediately stop functioning.
B. All network devices stop functioning in 30 days.
C. One AP Immediately stops functioning.
D. All APs stop functioning in 30 days.
What is a feature of distributed Layer 3 roaming?
A. An MX Security Appliance is not required as a concentrator.
B. An MX Security Appliance is required as a concentrator.
C. All wireless client traffic can be split-tunneled.
D. All wireless client traffic is tunneled.

Refer to the exhibit. What is the minimal Cisco Meraki Insight licensing requirement?
A. A single Meraki Insight license must be configured on network A to gain Web App Health visibility on network B.
B. A single Meraki Insight license must be configured on network B to gain Web App Health visibility on network B.
C. A single Meraki Insight license must be configured on network A, and a single license must be configured on network B, to gain Web App Health visibility on network B.
D. Two Meraki Insight licenses must be configured on network A to gain Web App Health visibility on network B.
E. Two Meraki Insight licenses must be configured on network A and a single license must be configured on network B, to gain Web App Health visibility on network B.
Air Marshal has contained a malicious SSID.
What are two effects on connectivity? (Choose two.)
A. Currently associated clients stay connected.
B. New clients can connect.
C. Currently associated clients are affected by restrictive traffic shaping rules.
D. New clients cannot connect.
E. Currently associated clients are disconnected.
Which order is accurate for a firmware upgrade on MX appliances in a high-availability configuration?
A. starts on the secondary MX appliance and then occurs on the primary MX appliance
B. starts on both MX appliances at the same time and then reboots both appliances after traffic on the primary MX appliance ceases
C. starts on both MX appliances at the same time and then immediately reboots both appliances
D. starts on the primary MX appliance and then occurs on the secondary MX appliance
Which three verbs of request are available in the Cisco Meraki API? (Choose three.)
A. SET
B. PUT
C. PATCH
D. ADD
E. POST
F. GET
A customer wants to use Microsoft Azure to host corporate application servers.
Which feature does the customer get by using a vMX appliance rather than connecting directly to Azure by VPN?
A. malware protection
B. SD-WAN
C. next-generation firewall
D. intrusion prevention
Which API endpoint clones a new Organization?
A. POST /organizations/clone/{organizationId}
B. PUT /organizations/{organizationId}/clone
C. POST /organizations/{organizationId}/new
D. POST /organizations/{organizationId}/clone
Which Cisco Meraki product must be deployed in addition to Systems Manager so that Systems Manager Sentry enrollment can be used?
A. MS Switch
B. Meraki Insight
C. MR Access Point
D. MV Smart Camera
Which information do the MXs in a High Availability pair share?
A. spanning-tree state
B. time synchronization state
C. DHCP association database
D. stateful firewall database
Which configuration step is necessary when automatic updating is required of iOS apps provisioned through Systems Manager that are found in the App Store?
A. No configuration step is necessary; automatic updating is the default behavior.
B. Configure automatic updating of iOS devices in the Meraki installed profile.
C. Create a security policy that enables automatic updates.
D. Create a profile with automatic update enabled and apply it to iOS devices.
