300-725 Online Practice Questions and Answers
What causes authentication failures on a Cisco WSA when LDAP is used for authentication?
A. when the passphrase contains only 5 characters
B. when the passphrase contains characters that are not 7-bit ASCI
C. when the passphrase contains one of following characters `@ # $ % ^'
D. when the passphrase contains 50 characters
Which two configuration options are available on a Cisco WSA within a decryption policy? (Choose two.)
A. Pass Through
B. Warn
C. Decrypt
D. Allow
E. Block
Which information in the HTTP request is used to determine if it is subject to the referrer exceptions feature in the Cisco WSA?
A. protocol
B. version
C. header
D. payload
What are all of the available options for configuring an exception to blocking for referred content?
A. all embedded/referred and all embedded/referred except
B. selected embedded/referred except, all embedded/referred, and selected embedded/referred
C. selected embedded/referred and all embedded/referred except
D. all embedded/referred, selected embedded/referred, and all embedded/referred except
By default, which two pieces of information does the Cisco WSA access log contain? (Choose two.)
A. HTTP Request Code
B. Content Type
C. Client IP Address
D. User Agent
E. Transaction ID
Which certificate format does a Cisco WSA need when HTTPS proxy is configured?
A. DER
B. CER
C. PEM
D. CRL
How does the Cisco WSA choose which scanning engine verdict to use when there is more than one verdict?
A. based on the least restrictive verdict
B. based on the most restrictive verdict
C. based on the first verdict returned
D. based on the last verdict returned
Which IP address and port are used by default to run the system setup wizard?
A. http://192.168.42.42:80
B. https://192.168.42.42:8080
C. https://192.168.42.10:8443
D. http://192.168.43.42:8080
Which two modes of operation does the Cisco WSA provide? (Choose two.)
A. connector
B. proxy
C. transparent
D. standard
E. explicit
Which two features on the Cisco WSA help prevent outbound data loss for HTTP or FTP traffic? (Choose two.)
A. web reputation filters
B. Advanced Malware Protection
C. third-party DLP integration
D. data security filters
E. SOCKS proxy
Which configuration mode does the Cisco WSA use to create an Active Directory realm for Kerberos authentication?
A. Forward
B. Connector
C. Transparent
D. Standard
An administrator wants to restrict file uploads to Facebook using the AVC feature.
Under which two actions must the administrator apply this restriction to an access policy? (Choose two.)
A. Monitor Facebook General
B. Monitor Social Networking
C. Monitor Facebook Photos and Videos
D. Monitor Facebook Messages and Chat
E. Monitor Facebook Application
What is a benefit of integrating Cisco WSA with TrustSec in ISE?
A. The policy trace tool can be used to match access policies using specific SGT
B. Traffic of authenticated users who use 802.1x can be tagged with SGT to identification profiles in a Cisco WSA
C. ISE can block authentication for users who generate multiple sessions using suspect TCP ports
D. Users in a specific SGT can be denied access to certain social websites.
When an access policy is created, what is the default option for the Application Settings?
A. Use Global Policy Applications Settings
B. Define the Applications Custom Setting
C. Set all applications to Block
D. Set all applications to Monitor
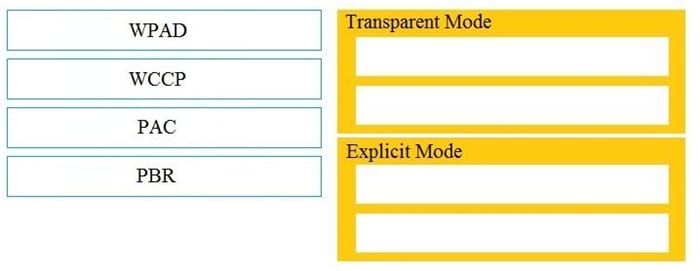
DRAG DROP
Drag and drop the Cisco WSA methods from the left onto the correct deployment modes on the right.
Select and Place: