250-440 Online Practice Questions and Answers
How are classes sorted in a traffic tree?
A. By service precedence
B. By priority, rate and average utilization
C. By parent, child, and sibling relationships
D. By server port number
Which PacketShaper report displays the percentage of bytes that are NOT retransmits?
A. The TCP Health graph
B. The Network Efficiency graph
C. The Normalized Network Delay graph
D. The Top 10 Classes graph
Why is Layer 5 through 7 traffic grouped together in the PacketShaper?
A. To work more easily with the Citrix priority tags
B. For ease of use with FTP, which is labeled by file name or extension
C. Because NNTP appears only by name or type of news group
D. To use for application classification
Which method does PacketShaper use to create child classes for Oracle databases?
A. Individually for each published application
B. Individually by encoding name
C. Once, for all Oracle traffic running on the subnet
D. Individually for each database that is discovered
Which CLI command will display the current rate and connection information about active hosts?
A. hostdb hosts
B. hostdb accounting
C. hostdb info
D. hostdb show
What partitions could an administrator apply to a class in the Sky UI?
A. You can apply any supported partitions and policies from the Sky UI
B. You can apply any supported partition from the Sky UI, but you must apply policies from the Advanced UI
C. You cannot apply them from the Sky Ul, you must use the Advanced UI to apply policies and partitions
D. You can apply static or dynamic partitions, but not burstable ones from the Sky UI
Which three (3) criteria are to be specified in a matching rule? (Select three)
A. Service group
B. Diffserv marking
C. Traffic type
D. SSL URL P
E. Interface
F. VLAN identification
Which type of file can be backed up and used later to restore a PacketShaper configuration?
A. sys.cfg
B. basic.cfg
C. cmd.csv
D. config.ldi
Which element is missing from this class lest statement? # class test outbound 10.0.0.200:21 10.0.12.100:2000
A. Partition
B. Policy
C. Protocol
D. Traffic class
Refer to the exhibit.
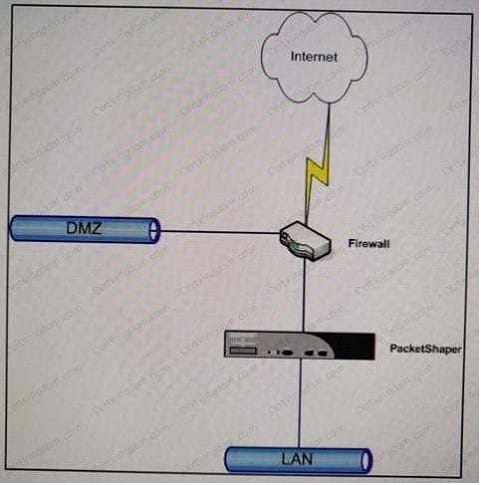
Which task must the administrator perform to make sure that traffic between (he IAN and DMZ is treated as pass-through PacketShaper installed as shown?
A. Create a class for LAN-to-DMZ traffic and apply a 100 MB partition to it. ..
B. Create a class for lANto-OMZ traffic and apply a 100-MB rate policy to it.
C. Create a class for lAN-tO-DMZ traffic and apply an ignore policy to it.
D. Configure the PacketShapet to automatically identify Inside and Outside hosts, therefor* no special configuration is required.
An administrator suspects that the primary Blue Coat Authentication and Authorization Agent (BCAAA)
server has stopped functioning. When checking the status of User Awareness on the Setup > User
Awareness page, the status message "In use" is displayed on the page.
What does the status "in use" mean?
A. The server is up. PadwtShaper has connected to the server and can look up users.
B. The server is busy. PacketShaper can't connect to It until it is freed up.
C. You configured the wrong IP address of the BCAA server on the PackefShaper. PacketShaper c3nl connect to the server.
D. The server is up. PacketShaper can connect to this server, but is using an alternate BCAAA server on your network.
Which statement accurately describes rate policies and priority policies?
A. Priority policies are most appropriate tor interactive traffic that is burstable
B. Rate polices apply only to non-IP traffic
C. Traffic classes without a specific policy assigned, are allocated no bandwidth
D. Traffic with rate policies are applied before the priority policy
What is the purpose of a "Traffic Class"?
A. It enforces the policy by normalizing all traffic
B. It applies source routing features for load balancing
C. It identities the traffic type, which allows a policy to be applied
D. It forwards traffic to the Measurement Engine
Which option allows an administrator to differentiate Citrix-based applications and protect their performance?
A. Choose Priority 7 from the matching rule's Citrix-specific classification criteria to identify print traffic.
B. Assign the default partition and policy to all parts of the Citrix traffic tree, regardless of application urgency.
C. Enable discovery and let PacketShaper discover the Citrix-based applications, then create a traffic class for each one.
D. When Citrix applications generate a large amount of print traffic, merge multiple Citrix-based applications into one traffic class
After insulting a PacketShaper inline between a switch and a router, communications are slow. Which command, executed repeatedly, can help to determine it there ate errors on the PacketShaper interfaces?
A. link show
B. net nic
C. tap health
D. traffic flow
