1Z0-1072-22 Online Practice Questions and Answers
Which statement is true about interconnecting Virtual Cloud Network (VCN)?
A. VCNs support transitive peering.
B. Peering VCNs should not have overlapping CIDR blocks.
C. VCNs must be in the same tenancy to be peered.
D. The only way to interconnect VCNs is through peering.
Which two statements are true about restoring a volume from a block volume backup in Oracle Cloud Infrastructure Block Volume service?
A. You can restore a volume from any full volume backup but not from an Incremental backup.
B. You can only restore a volume to the same availability domain in which the original block volume resides.
C. You can restore a block volume backup to a larger volume size.
D. You can restore a volume to any availability domain within the same region where the backup is stored.
E. You can restore only one volume from a manual block volume backup.
You create an autoscaling configuration of Linux compute instances in Oracle Cloud Infrastructure (OCI).
You noticed that your application is running slow. After checking your compute instances, you noticed that
autoscaling is not launching additional instances,
even though the existing compute instances already have high memory usage.
How can you resolve this issue?
A. Modify the scaling policy to monitor memory usage and scale up the number of instances when it meets the threshold.
B. Modify the scaling policy to monitor CPU usage and scale up the number of instances when it meets the threshold.
C. Install the monitoring agent to all compute instances which will trigger the autoscaling group.
D. Install OCI SDK in all compute instances and create a script that will trigger the autoscaling event if there is high memory usage.
Which does NOT set a variable in Terraform?
A. Passing the variable with a var statement to Terraform
B. Setting the variable as key value pairs in a file in a subdirectory named tfvar
C. A default value in the variable declaration within a TF plan file
D. Setting the environment variable using a TF_VAR_ predicate in front of the variable name
Which two identity providers can your administrator federate with Oracle Cloud Infrastructure? (Choose two.)
A. Microsoft Active Directory
B. Oracle Identity Cloud Services
C. AWS Directory Services
D. Google Directory Federation Services
You need to transfer over 12 TB of data from on-premises to your cloud account. You started copying this data over the internet and noticed that it will take too long to complete. Without increasing the costs of your subscription, what is the recommended way to send this amount of data to your cloud account?
A. Use Data Transfer Service to send your data.
B. Split the data into multiple parts and use the multipart tool.
C. Use a 10 GB FastConnect line to send the data.
D. Send the data over a VPN IPsec tunnel.
E. Compress the data and use the multipart tool.
What is a valid option when exporting a custom image?
A. object storage URL
B. archive storage URL
C. file storage service
D. block volume
Your organization has deployed a large, complex application across multiple compute instances in Oracle
Cloud Infrastructure (OCI). These compute instances also have block volume storage attached to them.
You want to create a time consistent backup of these block volume storage.
Which implementation strategy should be used?
A. Create a manual backup of each volume
B. Use scripts available in OCI to backup block volume storage
C. Group volumes in a volume group first and then use available scripts in OCI
D. Group volumes in a volume group and create a manual backup of the volume group
Your on-premises hosted application uses Oracle database server. Your database administrator must have access to the database server for managing the application. Your database server is sized for seasonal peak workloads, which results in high licensing costs. You want to move your application to Oracle Cloud Infrastructure (OCI) to take advantage of CPU scaling options. Which database offering on OCI would you select?
A. bare metal DB systems
B. VM DB systems
C. Autonomous Transactions Processing (ATP)
D. Autonomous Data Warehouse (ADW)
Which two choices are true for Autonomous Data Warehouse (ADW)? (Choose two.)
A. Billing stops only when the ADW is terminated
B. Billing stops for both CPU usage and storage usage when ADW is stopped
C. Billing for compute stops when ADW is stopped
D. Billing for storage continues when ADW is stopped
You are an administrator with an application running in Oracle Cloud Infrastructure (OCI). The company has a fleet of OCI compute virtual instances behind an load balancer. The load balancer backend set health check API is providing a 'Critical' level warning. You have confirmed that your application Is running healthy on the backend servers. What Is the possible reason for this 'Critical' warning?
A. The load balancer listener is not configured correctly.
B. The security list associated with the subnet In which the backend server is provisioned does not include the IP range for the source of the health check requests.
C. A user does not have correct Identity and Access Management (IAM) credentials on the backend servers.
D. The route table associated with the subnet in which the backend server is provisioned does not include the route for the OCI load balancer.
Which two statements are true regarding cloning a block volume?
A. You can change the block volume performance when creating a clone
B. You can clone block volumes across regions
C. You can change the block volume size when creating a clone
D. You can skip block volume encryption when creating a clone
You have launched a compute instance running Oracle database in a private subnet in the Oracle Cloud Infrastructure US East region. You have also created a Service Gateway to back up the data files to OCI Object Storage in the same region. You have modified the security list associated with the private subnet to allow traffic to the Service Gateway, but your instance still cannot access OCI Object Storage. How can you resolve this issue?
A. Add a stateful rule that enables ingress HTTPS (TOP port 443) traffic to 001 Object Storage in the security list associated with the private subnet
B. Add a stateful rule that enables egress HTTPS (TCP port 443) traffic to OCI Object Storage in the security list associated with the private subnet
C. Add a rule in the Route Table associated with the private subnet with Target type as "Service Gateway" and destination service as all IAD services in the Oracle Service Network.'
D. Use the default Security List, which has ports open for OCI Object Storage
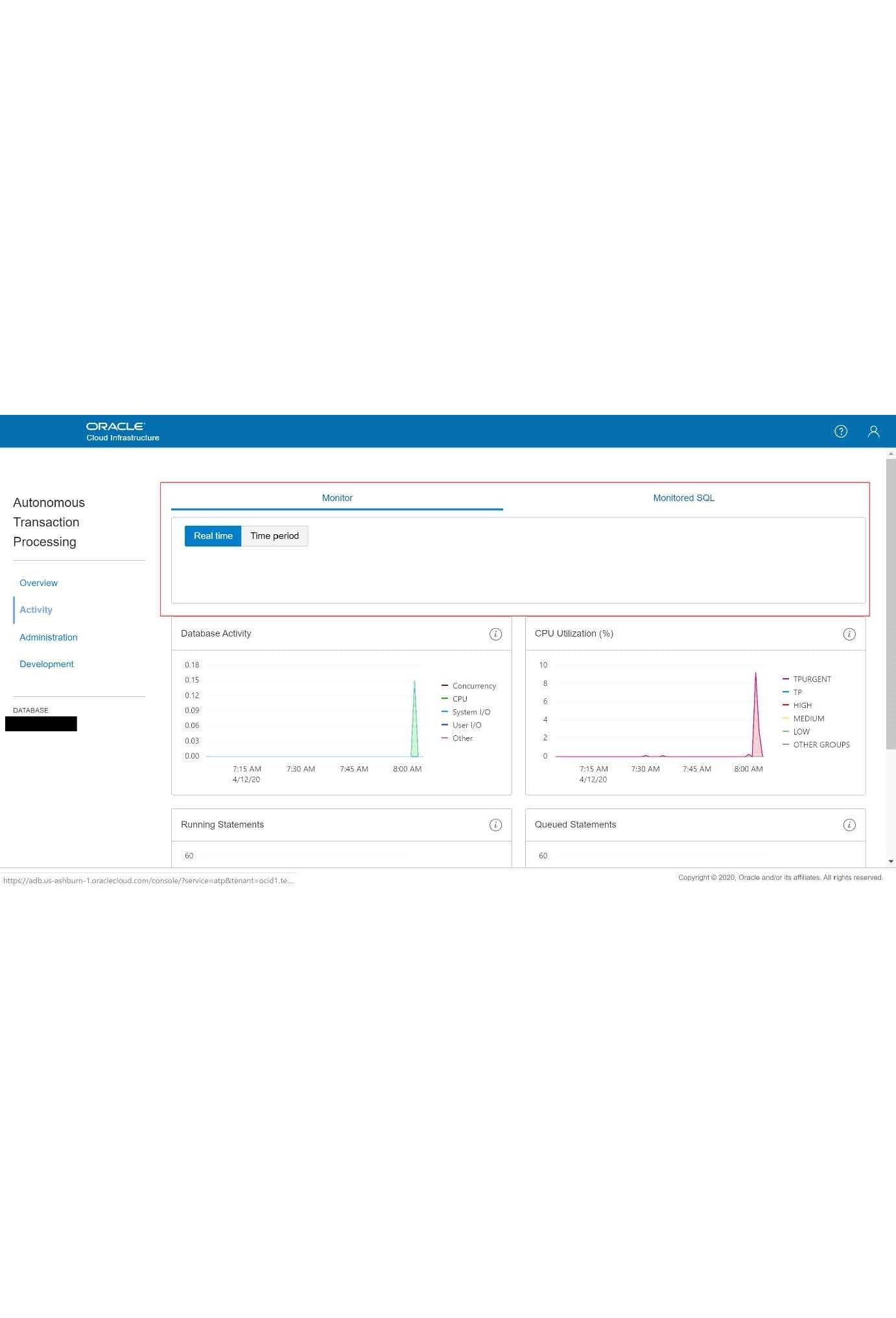
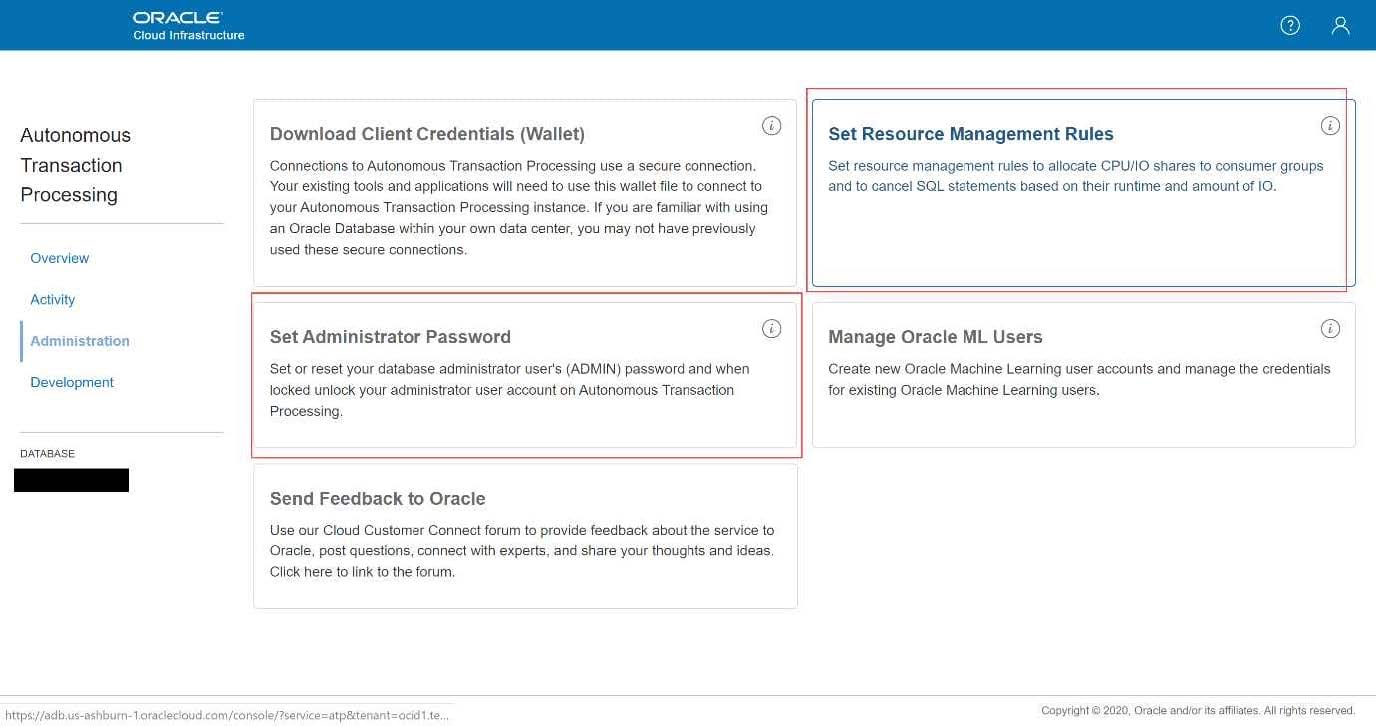
Which two options are available within the service console of Autonomous Transaction Processing?
A. Monitor the health of the database server including CPU, memory and query performance
B. Configure resource management rules and reset the admin password
C. Perform a manual backup of the ATP database
D. Fine tune a long running query using optimizer hints
Which of the following two tasks can be performed in the Oracle Cloud Infrastructure Console for Autonomous Data Warehouse?
A. Adjust Network Bandwidth
B. Scale up/down Memory
C. Increase Storage allocated for Database
D. Scale up/down CPU