1Z0-591 Online Practice Questions and Answers
The highest sales amount for this year is $10,000. If you create a rank measure for sales this year and display it on a report, the value will be________.
A. $10,000
B. 0
C. 1
D. Year
Which installation option is used to install into an existing Fusion Middleware Home?
A. Software Only Install
B. Simple Install
C. Enterprise Install
D. Cannot install into an existing Fusion Middleware Home
What is an example of a Session Variable?
A. ETL Load Date
B. User Organization
C. OLAP DSN
D. Top Customers by Revenue
WLS Embedded LDAP Server is managed by the Admin Server Console and supports which three options?
A. Creating and Maintaining Users
B. Authentication and Authorization
C. Basic Directory for storing user details
D. Subject area and row-level security, connection pool passwords
E. Application of Session Variables as Data Filters
An organization has re-implemented one of its systems but has not moved history. One database has data for all years up to 2010 and the other has data for years from 2011 to the present. The organization needs data from the years 2010
and 2011 on a single report.
How can you model this in the RPD?
A. By creating two Logical Fact Tables for each database
B. By creating joins in the physical model so it looks like a single table
C. By creating two logical table sources, that specify in Content tab using the Fragmentation content areas to specify the years for each source
D. By creating two logical table sources and checking the "This Source should be combined with other sources at this level" box leaving the Fragmentation content area blank.
E. By creating one logical table sources and checking the "This Source should be combined with other sources at this level" box
Select the correct statement.
A. Cache provides fast and always up-to-date information.
B. Cache can increase traffic to back end database.
C. Cache needs to be purged to refresh data.
D. Cache can degrade query performance by reading data from the disk instead of the database.
E. Cache is seeded by manually running PL/SQL at the back end database.
What are the two types of Session Variables?
A. System
B. Non System
C. Static
D. Dynamic
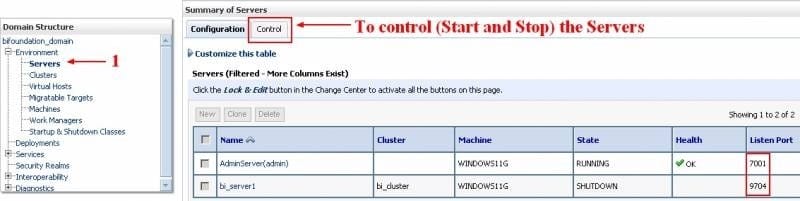
The WebLogic Console will allow you to perform which of the following functions in the BI Managed Server?
A. Start and Stop BI Services
B. Build Aggregate Queries
C. Create Summary Tables
D. Manage user logins
Which Oracle Partner is the supplier of map-based content to provide background maps, boundary information, and points of interest?
A. Navteq
B. TeleAtlas
C. Google
D. ESRI
The Consistency Checker checks______.
A. The validity of objects outside the metadata using the connection
B. Mappings to the physical objects
C. For objects deleted from the database
D. Syntax errors in derived logical columns
The three metadata layers are an important concept of the BI Server. Which statement is incorrect?
A. The physical layer defines the objects and relationships that the Oracle BI Server needs to write native queries against each physical data source.
B. Separating the logical of the application from the physical model provides the ability to federate multiple physical sources to the same logical object.
C. The model and mapping layer define the business or logical model of the data. This layer determines the analytic behavior seen by users.
D. The presentation layer defines the relationship that is needed to create the DML.
Which variable does not use initialization blocks to initialize its values?
A. Static Repository Variable
B. Dynamic Repository Variable
C. System Variable
D. Non System Variable
Oracle BI Server cache setup information is configured by using Enterprise Manager Fusion Middleware control. Which component stores the configuration Information?
A. NQSConfig.ini
B. Cache table in OBIEE repository
C. Web Catalogue
D. Instanceconfig.xml
Which analysis features could be applied to provide interactive controls for end users?
A. Column Selector
B. Action Links
C. Conditional Formatting
D. Narrative View
E. Greenbar Styling
If a customer is planning on building a data warehouse, how would you describe data warehousing to the customer?
A. The data in the data warehouse describes events and statuses of business processes, products and services, goals and organizational units, and generally mirrors every aspect of the structure and behavior of the organization.
B. Data warehouses can only be based on multidimensional data modeling.
C. Application based data warehouses can be bought off the shelf and used without any tweaking.
D. Data warehouse projects are usually implemented within two weeks.