4A0-100 Online Practice Questions and Answers
Which of the following best describes an Ethernet bridge?
A. A passive device simply used to connect two or more cables. Does not generate or amplify any signals.
B. A device that receives and retransmits a signal out its other ports, but does not do any Layer 2 analysis of the data.
C. A device that receives a signal and based on the Layer 2 destination address, makes a decision on which ports the signal should be retransmitted.
D. A device that receives a signal and based on the Layer 3 destination address, makes a decision on which ports the signal should be retransmitted.
What information is used to separate VLANs on a VLAN trunk that connects multiple VLANs?
A. VLAN tag.
B. IP Header.
C. FCS.
D. Priority Value.
A network administrator is creating a subnet plan for the address 172.16.0.0/16. The network must support 459 hosts on each subnet while providing the maximum number of subnets. What subnet mask should be used?
A. 255.255.0.0
B. 255.255.128.0
C. 255.255.224.0
D. 255.255.254.0
What is the function of the Routing Table Manager?
A. Based on the metrics of the routing protocol, find the best path to the destination network and install it in the routing table.
B. Provide a CLI interface to allow the operator to configure the dynamic routing protocol on the router.
C. Based on the routing protocol preference values, chose the route with the lowest preference and install it in the routing table.
D. Provide a CLI interface to allow the network operator to install static routes in the routing table.
Which of the following is NOT a field in a TCP header?
A. Source port.
B. MTU.
C. Sequence number.
D. Acknowledgement number.
E. Window size.
How does a VPRN service avoid the problem of overlapping IP addresses from different customers?
A. You cannot have overlapping IP addresses. Customers must change their IP address assignment.
B. Each VPRN service maintains a separate VPN routing and forwarding instance to separate customer routing information. This allows for overlapping addresses.
C. A VPRN ignores IP addressing information and uses MAC addressing instead, which are always unique.
D. A VPRN translates customer IP addresses to a private addressing scheme administered by the service provider.
Which of the following statements is FALSE when describing a Virtual Private LAN Service?
A. A VPLS emulates a virtual switch or bridge.
B. The VPLS performs MAC learning on MAC addresses seen from SAPs and SDPs.
C. When a VPLS receives a frame with an unknown MAC destination, the frame will be dropped.
D. MAC address forwarding database (FDB) is maintained for each VPLS.
Which of the following statements are TRUE about the Nokia SR 7750? (Choose 2)
A. It can boot without a compact flash in the CF3 slot.
B. It cannot boot without a compact flash in the CF3 slot.
C. It can operate without a compact flash in the CF3 slot once it has booted.
D. It cannot operate without a compact flash in the CF3 slot once it has booted.
How is Ethernet II different from Ethernet 802.3?
A. Ethernet II can be used on broadcast networks where as 802.3 was designed for point-to-point networks.
B. Ethernet II identifies its payload type where as 802.3 indicates the frame length.
C. Ethernet II identifies its frame length while 802.3 indicates the payload type.
D. Ethernet II and Ethernet 802.3 are two different names for the same protocol.
What is the function of a Routing Table Manager (RTM)?
A. To find the best path to the destination network and install it in the routing table - based on the metrics of the routing protocol.
B. To provide a CLI interface that allows the operator to configure the dynamic routing protocol on the router.
C. To choose the route with the lowest preference and install it in the routing table - based on the routing protocol preference values.
D. To provide a CLI interface that allows the network operator to install static routes in the routing table.
Which field in the TCP header is used by the receiver to indicate the number of segments it can receive?
A. Checksum
B. SYN
C. Destination port
D. Window size
E. MTU
A switch with the MAC FDB shown in the exhibit receives an Ethernet frame with source MAC address 00:00:8c:01:00:0a and destination MAC address ff:ff:ff:ff:ff:ff. On which ports is the frame forwarded?
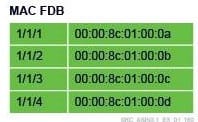
A. Only on port 1/1/1.
B. On all ports except 1/1/1.
C. On all four ports.
D. On none of the ports.
Which of the following is a characteristic of a subnet created with a prefix length of /32?
A. The subnet has only one address reserved for a loopback interface or the system interface.
B. The subnet has a broadcast address.
C. The subnet is configured for a point-to point link.
D. The subnet is reserved for a multicast address groups.
What is the next-hop address used on router R1 to configure a static route to the network on CR1?
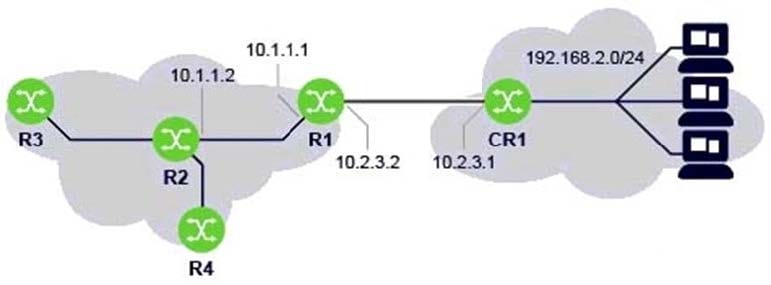
A. 10.2.3.2
B. 10.1.1.1
C. 10.2.3.1
D. 192.168.2.0
On what type of device is a Service Access Point (SAP) defined?
A. On the CE device.
B. On the PE device.
C. On the P device.
D. On both CE and PE devices.
