DEA-1TT4 Online Practice Questions and Answers
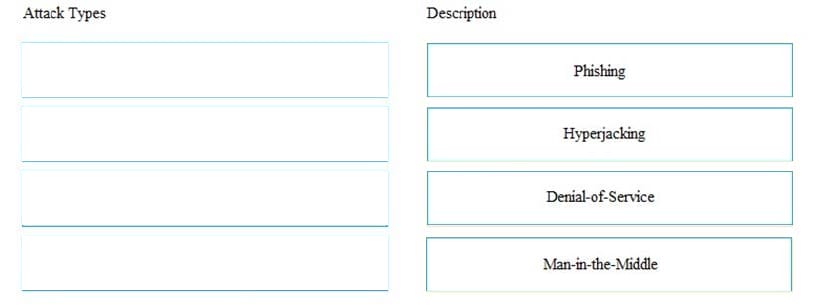
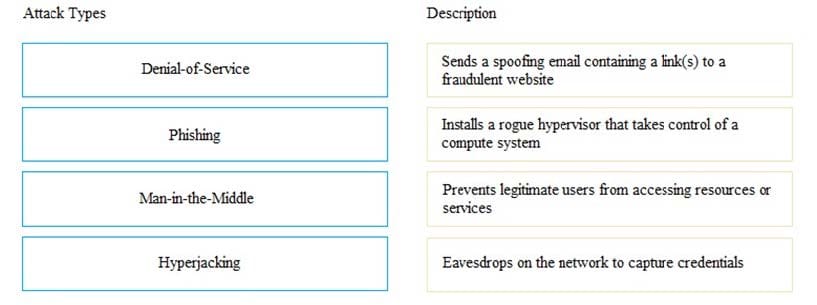
DRAG DROP
Match the types of attack with their respective description.
Select and Place:
What is a key advantage of cloning a virtual machine (VM)?
A. Ability to run new VMs simultaneously with the same IP address.
B. Reduces the time required to create multiple copies of a VM.
C. Improves the performance of an existing VM and new VMs.
D. Eliminates the need to create multiple snapshots for a VM.
What is a function of the metadata service in an object-based storage device (OSD)?
A. Generates the file system namespace from the file contents.
B. Manages both physical and logical disks on which the user data is stored.
C. Manages the storage space for all remote clients.
D. Maintains the object IDs and file system namespace mappings.
What does an area ID represent in Fibre Channel (FC) addressing?
A. Group of switch ports
B. Switch within a group
C. Port within a group
D. Group of switches
Which Internet of Things (IoT) component is responsible for the automation of operations by applying a force based on the dynamics of data?
A. Actuator
B. Switch
C. Sensor
D. Gateway
A backup administrator has defined a backup policy. The policy requires full backups to be performed at 10 PM every Sunday and incremental backups performed at 10 PM the remaining days. If files were accidentally deleted Wednesday morning, how many backup copies are required to restore the files?
A. 2
B. 3
C. 4
D. 5
When using a bridged iSCSI connection, which components facilitate communication between gateways?
A. Compute system with iSCSI ports and the storage system with Ethernet ports.
B. Compute system with iSCSI ports and the storage system with only FC ports.
C. Compute system with FC HBA ports and the storage system with only FC ports.
D. Compute system with FCoE ports and the storage system with iSCSI ports.
Based on the exhibit, what does the "X" represent in the FCIP tunnel configuration?
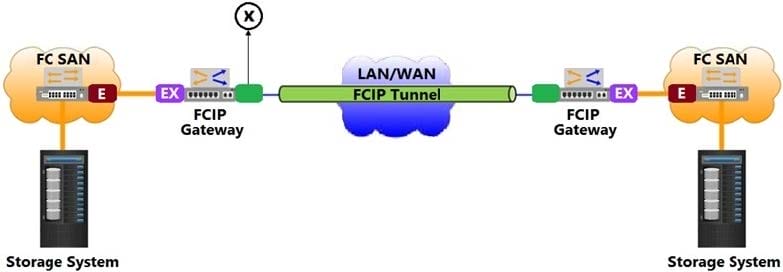
A. VX_port
B. EX_port
C. F_port
D. VE_port
If a company has experienced a passive attack on its IT infrastructure, how is the company's security impacted?
A. Access to services is denied.
B. Availability of data is affected.
C. Information privacy is compromised.
D. Data is altered by an unauthorized user.
A company is planning to perform a cloud-based backup. They want to send their data over a public network to a cloud backup device. Which security control mechanism helps to protect the data from an attacker?
A. Multi-factor authentication
B. Demilitarized zone
C. Data shredding
D. Encryption
Which Dell EMC product provides a software-defined platform that supports both block and file storage services?
A. XtremIO
B. PowerMax
C. FAST VP
D. VPLEX
Why is it important for organizations to implement a backup solution in a data center environment?
A. Improve the integrity of critical data
B. Ensure the availability of production data
C. Minimize the cost of data protection
D. Reduce redundant data in a production environment
Which Converged Network Adapter (CNA) component encapsulates Fibre Channel (FC) frames into Ethernet frames?
A. PCIe Bus
B. Fibre Channel HBA
C. Fibre Channel Forwarder
D. FCoE ASIC
What is a benefit of using an existing IP-based network infrastructure for storage connectivity?
A. Provide a dedicated network for storage
B. Provide the ability to extend the network over long distances
C. Ensure lossless transmission of FC traffic over Ethernet
D. Ensure security by allowing only localized data movement
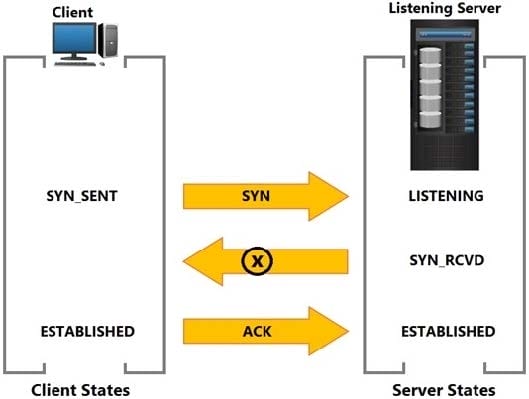
Based on the exhibit, what does the "X" represent?
A. NACK SYN
B. ACK SYN
C. SYN NACK
D. SYN ACK