CompTIA CAS-003 dumps - 100% Pass Guarantee!
Vendor: CompTIA
Certifications: CompTIA Advanced Security Practitioner
Exam Name: CompTIA Advanced Security Practitioner (CASP+)
Exam Code: CAS-003
Total Questions: 791 Q&As ( View Details)
Exam retired ,new exam code replace: CAS-004

- Q&As Identical to the VCE Product
- Windows, Mac, Linux, Mobile Phone
- Printable PDF without Watermark
- Instant Download Access
- Download Free PDF Demo
- Includes 365 Days of Free Updates
VCE
- Q&As Identical to the PDF Product
- Windows Only
- Simulates a Real Exam Environment
- Review Test History and Performance
- Instant Download Access
- Includes 365 Days of Free Updates
CompTIA CAS-003 Last Month Results
 96.6% Pass Rate
96.6% Pass Rate 365 Days Free Update
365 Days Free Update Verified By Professional IT Experts
Verified By Professional IT Experts 24/7 Live Support
24/7 Live Support Instant Download PDF&VCE
Instant Download PDF&VCE 3 Days Preparation Before Test
3 Days Preparation Before Test 18 Years Experience
18 Years Experience 6000+ IT Exam Dumps
6000+ IT Exam Dumps 100% Safe Shopping Experience
100% Safe Shopping Experience
CAS-003 Q&A's Detail
| Exam Code: | CAS-003 |
| Total Questions: | 791 |
| Single & Multiple Choice | 777 |
| Drag Drop | 5 |
| Hotspot | 1 |
| Simulation Labs | 8 |
CertBus Has the Latest CAS-003 Exam Dumps in Both PDF and VCE Format
- CompTIA_certbus_CAS-003_by_Selim_751.pdf
- 248.37 KB
- CompTIA_certbus_CAS-003_by_DarkMatter_639.pdf
- 233.84 KB
- CompTIA_certbus_CAS-003_by_Sulayman_Bah_667.pdf
- 254.7 KB
- CompTIA_certbus_CAS-003_by_dj_iv_710.pdf
- 224.52 KB
- CompTIA_certbus_CAS-003_by_CCIE70000_775.pdf
- 224.62 KB
- CompTIA_certbus_CAS-003_by_Ernest?_725.pdf
- 536.17 KB
CAS-003 Online Practice Questions and Answers
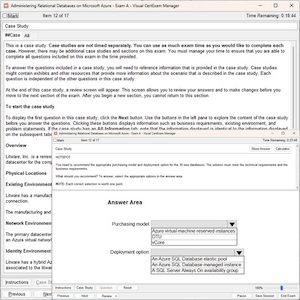
An administrator wishes to replace a legacy clinical software product as it has become a security risk. The legacy product generates $10,000 in revenue a month. The new software product has an initial cost of $180,000 and a yearly maintenance of $2,000 after the first year. However, it will generate $15,000 in revenue per month and be more secure. How many years until there is a return on investment for this new package?
A. 1
B. 2
C. 3
D. 4
A consulting firm was hired to conduct assessment for a company. During the first stage, a penetration tester used a tool that provided the following output:
TCP 80 open
TCP 443 open
TCP 1434 filtered
The penetration tester then used a different tool to make the following requests:
GET / script/login.php?token=45$MHT000MND876
GET / script/login.php?token=@#984DCSPQ%091DF
Which of the following tools did the penetration tester use?
A. Protocol analyzer
B. Port scanner
C. Fuzzer
D. Brute forcer
E. Log analyzer
F. HTTP interceptor
A medical device company is implementing a new COTS antivirus solution in its manufacturing plant. All validated machines and instruments must be retested for interoperability with the new software. Which of the following would BEST ensure the software and instruments are working as designed?
A. System design documentation
B. User acceptance testing
C. Peer review
D. Static code analysis testing
E. Change control documentation
A security analyst receives an email from a peer that includes a sample of code from a piece of malware found in an application running in the organization's staging environment. During the incident response process, it is determined the code was introduced into the environment as a result of a compromised laptop being used to harvest credentials and access the organization's code repository. While the laptop itself was not used to access the code repository, an attacker was able to leverage the harvested credentials from another system in the development environment to bypass the ACLs limiting access to the repositories. Which of the following controls MOST likely would have interrupted the kill chain in this attack?
A. IP whitelisting on the perimeter firewall
B. MFA for developer access
C. Dynamic analysis scans in the production environment
D. Blue team engagement in peer-review activities
E. Time-based restrictions on developer access to code repositories
A company wants to secure a newly developed application that is used to access sensitive information and data from corporate resources The application was developed by a third- party organization, and it is now being used heavily despite lacking the following controls:
1.
Certificate pinning
2.
Tokenization
3.
Biometric authentication
The company has already implemented the following controls:
1.
Full device encryption
2.
Screen lock
3.
Device password
4.
Remote wipe
The company wants to defend against interception of data attacks Which of the following compensating controls should the company implement NEXT?
A. Enforce the use of a VPN when using the newly developed application.
B. Implement a geofencing solution that disables the application according to company requirements.
C. Implement an out-of-band second factor to authenticate authorized users
D. Install the application in a secure container requiring additional authentication controls.
Add Comments
Success Stories
- United Arab Emirates
- Xsen
- Apr 13, 2024
- Rating: 4.1 / 5.0
![]()
I passed this exam. The questions are the same, read it carefully. Answer sequence may change to confuse you. But questions and answers are the same.
- India
- dre
- Apr 10, 2024
- Rating: 4.4 / 5.0
![]()
With the help of this dump, I passed the exam perfectly. Thanks a lot.

 Printable PDF
Printable PDF